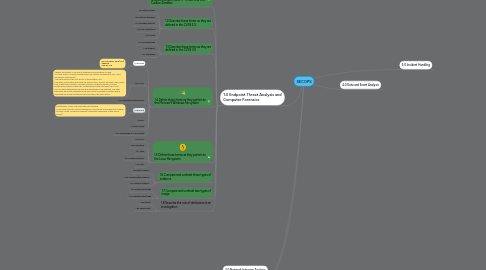
1. 1.0 Endpoint Threat Analysis and Computer Forensics
1.1. 1.1 Interpret the output report of a malware analysis tool such as AMP Threat Grid and Cuckoo Sandbox
1.2. 1.2 Describe these terms as they are defined in the CVSS 3.0:
1.2.1. 1.2.a Attack vector
1.2.2. 1.2.b Attack complexity
1.2.3. 1.2.c Privileges required
1.2.4. 1.2.d User interaction
1.2.5. 1.2.e Scope
1.3. 1.3 Describe these terms as they are defined in the CVSS 3.0
1.3.1. 1.3.a Confidentiality
1.3.2. 1.3.b Integrity
1.3.3. 1.3.c Availability
1.4. 1.4 Define these items as they pertain to the Microsoft Windows file system
1.4.1. 1.4.a FAT32
1.4.1.1. -File Allocation Table (FAT) -28bitow -max do 2TB
1.4.2. 1.4.b NTFS
1.4.2.1. -default file system in Microsoft Windows since Windows NT and is a more secure, scalable, and advanced file system compared to FAT. NTFS has several components. -The boot sector is the first sector in the partition, and it contains information about the file system itself, such as the start code, sector size, cluster size in sectors, and the number of reserved sectors. The file system area contains many files, including the master file table (MFT). The MFT includes metadata of the files and directories in the partition. The data area holds the actual contents of the files, and it is divided in clusters with a size assigned during formatting and recorded in the boot sector.
1.4.3. 1.4.c Alternative data streams
1.4.4. 1.4.d MACE
1.4.4.1. Timestamps, MACE, and Alternate Data Streams NTFS keeps track of lots of timestamps. Each file has a timestamp for Modify, Access, Create, and Entry Modified (commonly referred to as the MACE values).
1.4.5. 1.4.e EFI
1.4.6. 1.4.f Free space
1.4.7. 1.4.g Timestamps on a file system
1.5. 1.5 Define these terms as they pertain to the Linux file system
1.5.1. 1.5.a EXT4
1.5.2. 1.5.b Journaling
1.5.3. 1.5.c MBR
1.5.4. 1.5.d Swap file system
1.5.5. 1.5.e MAC
1.6. 1.6 Compare and contrast three types of evidence
1.6.1. 1.6.a Best evidence
1.6.2. 1.6.b Corroborative evidence
1.6.3. 1.6.c Indirect evidence
1.7. 1.7 Compare and contrast two types of image
1.7.1. 1.7.a Altered disk image
1.7.2. 1.7.b Unaltered disk image
1.8. 1.8 Describe the role of attribution in an investigation
1.8.1. 1.8.a Assets
1.8.2. 1.8.b Threat actor

