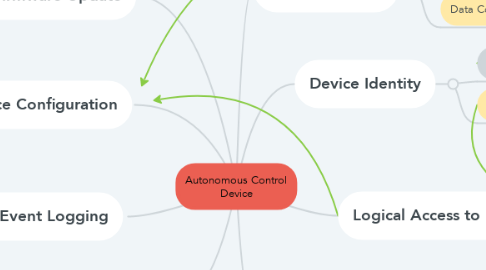
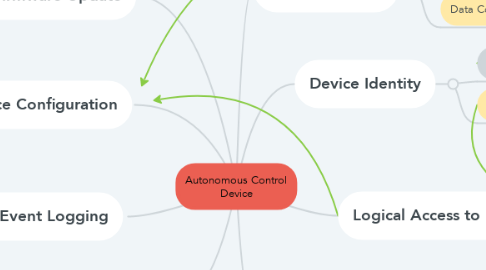
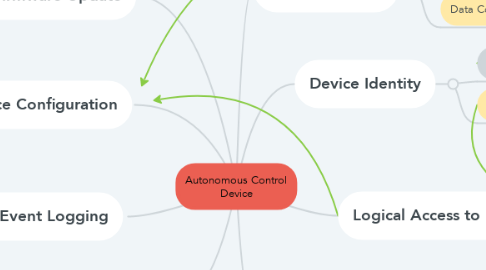
Autonomous Control Device
by bryan owen
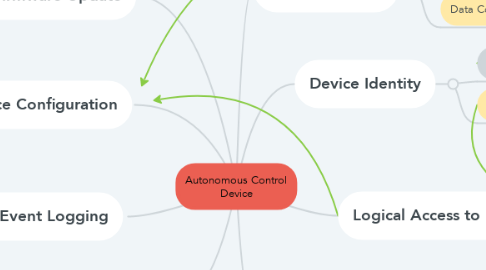
1. Device Configuration
1.1. Defense in Depth
1.2. Resource Availability
2. Software and Firmware Update
2.1. Renewable Security
3. Cybersecurity Event Logging
3.1. Timely Response to Events
3.2. Failure Reporting
4. Small Trusted Computing Base
5. Exploring core cybersecurity property relationships for autonomous devices [Dec 2019 B. Owen]
5.1. ISA/IEC 62243
5.2. NIST IR 8259
5.3. MSR-TR-2017-16
6. Device Identity
6.1. Hardware-based Root of Trust
6.2. Identification and Authentication Control
7. Data Protection
7.1. System Integrity
7.2. Data Confidentiality
8. Logical Access to Interfaces
8.1. Use Control
8.2. Restricted Data Flow
8.3. Certificate-based Authentication
9. Compartmentalization