1. No safe place
1.1. Your laptop is not safe laying around. You would not leave cash lying around, so do not leave your laptop laying around. Conferences of any description are a prime target of thieves, as they know that the attendees guards are often down, and will leave laptops laying around. Thieves rely on this false sense of security to steal them.
2. Cable lock
2.1. Most laptops have a Universal Security Slot (USS), also known as a Kensington Security Slot (sometimes referred to as a K-slot or Kensington Slot). Will it stop bolt cutters? Unlikely. Will it stop a casual thief that just happened to be walking past your hotel room while room service had propped the door open, and then gone off to get more towels? Probably. And make sure to secure it around a strong, immovable, indestructible object. Also use it in the office. What percentage of laptop thefts occur in the office? (See below for answer).
3. art
3.1. Laptops and mobile gadgets like cell phones, PDAs, and USB flash drives have become a necessity in many business settings
3.2. And such equipment now spends more time than ever outside the office, as employees work at home or in the nearest Starbucks.
3.3. this dramatically increase the likelihood of loss or theft, now that devices are outside corporate premises
3.4. laptop thefts out of parked cars and conference rooms may grab headlines
3.5. but a far greater number of devices simply get left behind in places like cabs, subways, and airplanes
3.6. YouGetItBack.com reports that La Guardia airport alone has accumulated more than 70,000 unclaimed laptops and PDAs in its lost and found.
3.7. According to Accenture, 10 to 15 percent of all handheld computers, PDAs, mobile phones, and pagers are eventually lost by their owners.
3.8. A 2006 Ponemon Institute study reported an 81 percent increase in the number of companies reporting stolen laptops between 2005 and 2006. Even notebooks that never leave the office can be targets, as many thefts are inside jobs.
3.8.1. insider threat
3.9. if you lose your data
3.9.1. But the files on the machine may raise more-troubling issues: They can hold trade secrets or financial and customer data; they may not be backed up on a central server; and losing them may trigger embarrassing public reporting requirements under several recent federal and state laws.
3.10. According to a 2007 survey by McAfee and Datamonitor, a data breach involving personal customer information could cost a company, on average, $268,000 in reporting expenses--even if the data is never used. And one-third of the companies surveyed said that a major security breach had the potential to put them out of business entirely.
3.11. how to greatly reduce loss of device and its data
3.11.1. ID each device and register with a recovery service
3.11.1.1. An astonishingly large number of businesses never record even the serial numbers of their equipment, police say, making it impossible for authorities to reunite found items with their rightful owners.
3.11.1.2. asset inventory
3.11.1.2.1. at least in case of insurance claims.
3.11.1.3. Vendors that offer labeling and recovery services include ArmorTag, BoomerangIt, StuffBak, TrackItBack, YouGetItBack.com, and zReturn.
3.11.1.4. The recovery firms unanimously cite privacy considerations and their 24-hour phone service as reasons to use their labels instead of just a taped-on business card or an inventory tag from your own company.
3.11.2. Rely on Recovery Software
3.11.2.1. tracking utilities that connect periodically to a central server.
3.11.2.2. When any of these does so, the associated service can trace your laptop's location on the Internet and summon the local police to recover it.
3.11.2.3. Some tracking products also have such features as the ability to wipe out key data if a laptop is stolen
3.11.2.4. vendors
3.11.2.4.1. Absolute Software's ComputraceComplete ($50 per year), Brigadoon's PC PhoneHome ($30 lifetime), Inspice's Inspice Trace ($30/year), XTool's Laptop Tracker ($40 per year for Small Business Edition) and zTrace Technologies' zTrace Gold ($50 per year)
3.11.2.5. The laptop's location may be pinpointed by IP address or by GPS, depending on the device and the service
3.11.2.6. ComputraceComplete is the market leader
3.11.2.6.1. a remote data deletion capability that meets Department of Defense standards.
3.11.2.6.2. The company guarantees recovery of your computer within 30 days; if it fails to produce the lost unit, it will pay you 90 percent of the device's original purchase price, up to $1000.
3.11.3. Back Up and Encrypt Your Data
3.11.3.1. numerous inexpensive security tools that provide military-grade encryption.
3.11.3.2. But these programs are only as effective as their users allow them to be, so make sure that your business's employees understand how to take care of their equipment.
3.11.3.3. For instance, instead of letting a laptop sleep during travel, they should shut it down completely, thereby locking the drive.
3.11.4. Educate Your Employees
3.11.4.1. The human factor in laptop security may be the most important one
3.11.4.2. Most laptops are accidentally abandoned, not purloined, and even instances of actual theft usually amount to crimes of opportunity
3.11.4.3. Physical security is the single best way to prevent loss.
3.11.4.4. Unfortunately, persuading employees to guard company property with the same attention and zeal they would devote to their own purse or wallet is a difficult.
3.11.4.5. Develop a written company policy on safeguarding mobile equipment, and periodically reinforce awareness of the consequences of laptop theft.
3.11.4.6. Employees need to realize that they may lose, along with the laptop, their personal Web passwords and e-mail, any work not backed up, and whatever else they might have stowed in the laptop bag--such as keys, USB flash drives, and company papers.
3.11.4.7. Remind workers about the importance of taking personal responsibility for company property, and review the consequences of noncompliance.
3.11.4.8. Do periodic spot-checks to ensure that people are adhering to company guidelines.
3.11.4.9. Advise your notebook users to carry unobtrusive bags that don't scream "laptop inside."
3.11.4.9.1. Messenger bags, knapsacks, and rolling overnighters with inner pockets all make good alternatives to dedicated laptop bags.
3.11.4.10. Use devices such as "proximity" alarms.
3.11.4.10.1. The Belkin USB Laptop Security Alarm ($55) function as cable locks but sound an alarm if someone cuts the cable. The Doberman Laptop Defender Portable USB Computer Alarm ($30) incorporates a motion sensor that triggers a loud alarm if the device attached to it is moved.
3.11.4.11. Never leave your laptop unguarded in a hotel or conference room. Protect it by using a cable lock or a hotel safe. If neither of these is available, take the laptop with you.
3.11.4.12. At the office, lock portables in a special drawer or safe when you go home for the night.
3.11.4.13. Never leave a laptop bag on a car seat in plain view. Always lock it in the trunk--but do so out of the sight of others in the parking lot.
3.11.4.14. Triple-guard your bag at airports (one of the most common theft locations). When waiting at a gate, place your bag between your feet.
3.11.5. For less than $100 per machine, you can add tags, tracking software, and locking systems that may save you many times that amount.
4. Redbook
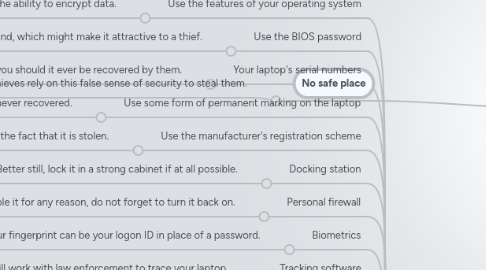
4.1. Use the features of your operating system
4.1.1. Use the features of your operating system If you have chosen an operating system that has in-built security features (Windows 2000 Professional and Windows XP Professional are examples) then do not be afraid to use them. Features may include secure logon, file level security, and the ability to encrypt data.
4.2. Use the BIOS password
4.2.1. t would be unwise not to protect the BIOS. Find out whether the BIOS will also protect the hard disk drive to stop it from being used in another machine. Another tip is to find out what the procedure is for resetting the BIOS password. If it has to be sent back to the manufacturer, so much the better, as that will afford some protection, as a thief is unlikely to do that. Some will offer an in-the-field work around, which might make it attractive to a thief.
4.3. Your laptop's serial numbers
4.3.1. It is written down, right? And stored in a safe place? Good. That will help the police return it to you should it ever be recovered by them.
4.4. Use some form of permanent marking on the laptop
4.4.1. Engraving your company name on the case of the laptop with an address or contact number, or both, may increase the likelihood of getting the laptop returned to you if it is stolen and recovered (or, if by some accident, you forget it). Commercial asset tags are also a great aid to the police to return the laptop to you. It may also serve as a deterrent to the casual thief if the choice is between stealing a marked laptop or an unmarked laptop. Why? They cannot sell it using an online auction so easily. Also, travelling through airport security means that someone is also less likely to pick up your laptop accidentally. Information freely available on the Web suggests that 97% of stolen laptops are never recovered.
4.5. Use the manufacturer's registration scheme
4.5.1. Most people ignore registration because they think that it is likely to lead to spam. However, remembering that thieves are usually not smart, one might be unintelligent enough to send it in for service or to reset the BIOS, so having it registered with the manufacturer might prove valuable if you alert them to the fact that it is stolen.
4.6. Docking station
4.6.1. Use a docking station that is securely fastened to your desk. If it also allows you to lock the laptop in place, so much the better. This is especially important if you are leaving the laptop overnight, or longer. Better still, lock it in a strong cabinet if at all possible.
4.7. Personal firewall
4.7.1. Use a third-party firewall to prevent hackers from hacking into your laptop, and maybe into the company network. If you do disable it for any reason, do not forget to turn it back on.
4.8. Biometrics
4.8.1. If your laptop has this capability, then familiarize yourself with them and then use them. Your fingerprint can be your logon ID in place of a password.
4.9. Tracking software
4.9.1. There are companies that offer tracking software, allowing your laptop to regularly ping a tracking center with a signal that allows it to be traced. If the laptop is stolen the company will work with law enforcement to trace your laptop.
4.10. Laptop case
4.10.1. It might look chic to have the latest designer laptop case or manufacturers case, but nothing sends out a better signal to a thief than an ostentatious display, which may include your company logo, elite looking luggage tags, your business card embossed in plastic that gives a thief a clue as to the likely worth of the contents. There are nondescript backpacks that have padded sleeves to hold a laptop safely. A backpack is useful for going to the restroom without having to put your case down. For the ultra-security conscious, buy little padlocks to lock the zips so that no-one can get into the backpack quickly, steal the laptop, and then zip it back up again.
4.11. Public places
4.11.1. Thieves are good at thieving. They will target coffee houses, cafes, restaurants, and the hotel lobby, as at some stage you will put your case on the floor, and your guard is usually let down as you place an order. This is especially true if you are paying for something by credit card, as you are busy keeping an eye on that, entering a PIN, signing, and your attention is elsewhere. Thieves can be as anonymous and as part of the scenery as you are.
4.12. Air travel
4.12.1. Anywhere that you have to put your laptop down you are at risk of getting your laptop stolen. Air travel provides a number of opportunities to a well-organized thief. Curb-side check-in, car rental, check-in, security checkpoints, shops, seating areas, and rest-rooms are all areas where extra caution should be taken.
4.13. Car travel
4.13.1. At some stage you are likely to rent a car, or travel in your own car. Never, ever, ever leave the case in full view on the back seat, front seat, floor wells, or anywhere that it is in view. If you know that you are going to have to lock it in the trunk/boot do it out of plain sight wherever possible. If you have an SUV, make sure that you use the laptop lock to secure it to the car, as the luggage compartment cover will provide no protection. If it has a trunk/boot lid and you are going to have to leave the laptop in the trunk, then do so before you get to your destination if that is possible. Thieves will target restaurants or bars for business and watch for groups loading up the trunk/boot with laptops. If possible, load the trunk before you leave for the restaurant/bar. If there is a way that you can secure your laptop to the trunk lid with the cable then do not be frightened to do so. Thieves will target rental vehicles. Also, if the vehicle is damaged you will probably be liable for that too.
4.14. Hotels
4.14.1. Always secure the laptop in the hotel room. Doors can often be left open by hotel staff, and they can sometimes be conned into letting thieves into your room. If you have to leave it in the hotel safe (if there is one) then get a receipt. If you lock it in your room safe, before you do so, ask what the override process is if you forget the key code combination. Do not leave it with hotel personnel. If you have to leave it in the hotel room for an extended period of time, lock it out of sight if possible.
4.15. Getting the security habit
4.15.1. Probably the weakest link in the security chain is the people. Which means you and me. If you can adopt a healthy siege mentality regarding your laptop, you will increase your chances of keeping it. It takes seconds to use the cable lock. Install it while the laptop is powering up. Make it part of your routine to install it. People may tease you for constantly locking it up, but thieves will not. And do not forget that it is not safe in the office either, so lock it up there, too.
4.16. Checkpoint security
4.16.1. t is a requirement at most airports to remove your laptop and put it on a plastic tray when going through security. Make sure that you have external identification marks on the top and bottom of your laptop to deter it being accidentally "stolen". If you are unfortunate enough to be required to give up your laptop be sure to get a receipt. Ask to see the identification of the security person requesting your laptop. Make a mental note of their name, number, and description. If you have shoes, bags, carry-ons, coats, and so on to go through the screener, be sure to put your laptop on the belt last. Do not walk through the body screener until you have seen your laptop disappear into the x-ray machine. This will prevent someone from stealing it before it goes through security. It also minimizes the possibility that someone will steal it on the other side before you get through. Maximize your chances to get through the screener before it does so that it is not just sitting there for someone else to grab.
4.17. 40% of laptop thefts occur in the office
4.18. Information freely available on the Web suggests that 97% of stolen laptops are never recovered.
4.19. 25 April 2007
5. some tech tips
5.1. The FAA recently learned of a hustle that's being employed at airports all across the country to steal laptop computers. It involves two persons who look for a victim carrying a laptop and approaching a metal detector. They position themselves in front of the unsuspecting passenger. They stall until the mark puts the laptop computer on the conveyor belt. Then the first subject moves through the metal detector easily. The second subject sets off the detector and begins a slow process of emptying pockets, removing jewelry, etc. While this is happening, the first subject takes the laptop as soon as it appears on the conveyor belt and moves away quickly. When the passenger finally gets through the metal detector, the laptop is gone. The subject that picks it up heads into the gate area and disappears among the crowd.
5.2. Phoenix BIOS TheftGuard is the first theft deterrent application that cannot be removed or replaced merely by installing another hard drive. The solution is digitally registered and installed in the Phoenix cME FirstBIOS and Host Protected Area (HPA), which is a secure environment independent of the operating system. If a registered machine is reported as stolen on the TheftGuard website, the next time the machine is connected to the Internet it will automatically send a signal which will verify it as stolen. The machine can then immediately be disabled, the IP address can be captured for tracking purposes and the data on the hard drive can even be deleted. Since TheftGuard is enabled through Phoenix cME FirstBIOS, the application will still be able to check for integrity of the application components even if a new hard drive is placed in the system. Also it does not depend on the operating system installed.
5.3. Homing Pigeon runs fully autonomously, it can get out of networks where browsing is blocked, it can get out of very hostile network situations, it can run periodically if desired, and report a myriad of information about the machine and thief. Also it includes format blocking and format recovery. Best of all, Homing Pigeon has no subscription fee. You buy it once for $39.95, and it will function for life. RC5DES
5.4. lots of little solutions
6. art
6.1. According to Safeware Insurance Agency (www.safeware.com), more than 600,000 laptops are stolen every year, which translates into an estimated $5.4 billion loss of proprietary information.
6.1.1. March 2008
6.2. According to the FBI, a whopping 97% of stolen computers never return to their rightful owner.
6.3. awareness key
6.3.1. “Never assume end users will remember all your policies. Put up posters, conduct security classes, give travelers a pretrip checklist on key security procedures to follow. Reinforce your policies at least yearly by conducting 60-minute security trainings.
6.3.2. reserve 15 minutes each quarter in department meetings
6.3.3. it is important to run occasional compliance spot checks and report your findings (both positive and negative) to supervisors.
6.3.4. an acceptable use policy is also in place.
6.3.5. Write up a policy on how end users need to take care of their computers both inside and outside the office.
6.4. lock down
6.4.1. diligently safeguarding the physical security of their laptops
6.4.2. Among the most common reported scenarios we see is the theft of notebooks left in plain view on car seats.
6.4.3. Lock your notebook in the trunk if you must leave it in the car and use a cable lock while you’re seated at a desk.”
6.4.4. most computers are stolen from cars, airports, and hotel rooms.
6.4.5. While traveling, store computers in a nondescript carrying case so as not to draw unwanted attention.
6.4.6. knowing where your notebooks are is more than half the battle for IT departments in SMEs who often do not have an enterprise-caliber IT asset management system.
6.4.7. “IT asset management systems are designed to track only those computers that are bolted to office desks—not out in the field. New Internet-based IT asset management products have changed all this.
6.4.8. Consider software that, once the stolen laptop is online, allows a computer to phone home for recovery by professionals or install disk wipe software that wipes the hard drive clean.”
6.5. Act now
6.5.1. when stolen
6.5.1.1. are things this bad?
6.5.1.1.1. report it immediately. He notes, “Time is of the essence to keep thieves from intruding on the company network. Have a plan in place that has a step-by-step approach to address all the issues involved with a data breach. By preparing for the worst, you can minimize your financial exposure.”
6.5.1.2. what do we do?
6.5.1.2.1. So what do you do if a notebook goes missing? Haidri says several products are designed to help locate and recover lost or stolen computers. “Talk to your computer manufacturer for their recommendations on the product that best suits your particular computer population,” he says. “The best products come complete with a recovery guarantee and utilize relationships with local police forces to find missing computers and prosecute thieves.”
7. Network Sentry
7.1. Security, of course, is not at the forefront of every employee’s mind.
7.2. Indeed, people take dumb chances
7.2.1. actually, accept bad risks
7.2.2. They leave machines unattended when they go to the rest room in a public venue
7.2.3. They leave them lying on the front seat of an unlocked car when they run into a store
7.3. 62% not even know laptop is missing
7.3.1. a study by Absolute Software that spotlights some disturbing malfeasance by respondents: 62 percent say that missing computers aren’t even noticed
