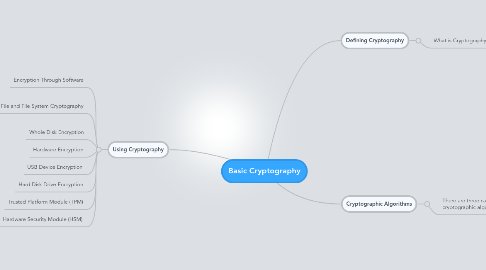
1. Using Cryptography
1.1. Encryption Through Software
1.2. File and File System Cryptography
1.2.1. Prett Good Privacy (PGP)
1.2.2. MS Windows Encrpting File System (EFS)
1.3. Whole Disk Encryption
1.4. Hardware Encryption
1.5. USB Device Encryption
1.6. Hard Disk Drive Encryption
1.7. Trusted Platform Module (TPM)
1.8. Hardware Security Module (HSM)
2. Defining Cryptography
2.1. What is Cryptography?
2.1.1. Cryptography and Security
2.1.1.1. Cryptography can provide five basic protections:
2.1.1.1.1. Confidentiality
2.1.1.1.2. Integrity
2.1.1.1.3. Availability
2.1.1.1.4. Authenticity
2.1.1.1.5. Nonrepudiation
3. Cryptographic Algorithms
3.1. There are three categories of cryptographic algorithms
3.1.1. Hash
3.1.1.1. Hashed Message Authentication Code (HMAC)
3.1.1.2. Message Digest (MD)
3.1.1.3. Secure Hash Algorithm (SHA)
3.1.1.4. Whirlpool
3.1.1.5. RACE Integrity Primitives Evaluation Message Digest (RIPEMD)
3.1.1.6. Password Hash
3.1.1.6.1. LM (LAN Manager)
3.1.1.6.2. NTLM (New Technology LAN Manager)
3.1.2. Symmetric Encryption aka Private key cryptography
3.1.2.1. Stream Cipher
3.1.2.2. Block Cipher
3.1.2.3. Data Encryption Standard (DES)
3.1.2.4. Triple Data Encryption Standard (3DES)
3.1.2.5. Advanced Encryption Standard (AES)
3.1.2.6. Other Algorithms
3.1.2.6.1. Rivest Cipher
3.1.2.6.2. Blowfish
3.1.3. Asymmetric Encryption aka Public key cryptography
3.1.3.1. RSA
3.1.3.2. Elliptic Curve Cryptography (ECC)
3.1.3.3. Quantum Cryptography
3.1.3.4. NTRUEncrypt
