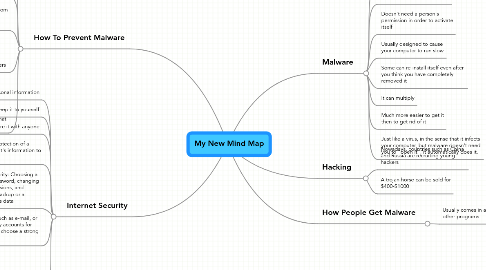
1. How To Prevent Malware
1.1. Make your computer notify you every time, a program is trying to be downloaded onto your computer
1.2. Have a anti-virus program installed onto your computer
1.2.1. Have it updated regulary.
1.3. Install a pop-up blocker
1.3.1. This can prevent malware from being downloaded
1.4. Don't download programs or software from unknown sites, chances are they contain malware
1.5. Be careful when you are sharing your files with others
1.5.1. If the orginal computer contained malware, and you shared something with another user, that computer can get infected too.
1.5.2. Why ? Malware muliplies, it can implant itself on a disk or file
1.6. Read the fine print on what you are downloading
1.6.1. Most of the time people don't read the fine print on what they download
1.6.2. Sometimes you are allowing the program to install malware onto your computer
2. Internet Security
2.1. Includes personal information
2.2. Always keep it to yourself
2.3. Don't share it with anyone
2.4. Involves the protection of a computer and it's information to unknown users
2.5. Basic Security: Choosing a strong password, changing file permissions, and having a backup or a computer's data
2.6. When have accounts such as e-mail, or online banking, or ebay accounts for example, make sure to choose a strong password
2.7. Virus + Worm
2.7.1. They are both made to infect your computer
2.7.2. Easier to receive then to get rid of
2.7.3. Virus needs someone to "open" it or activate it
2.7.4. Worm automatically opens itself
3. Malware
3.1. Type of software
3.2. Made to infect other peoples computer
3.3. Doesn't need a person's permission in order to activate itself
3.4. Usually designed to cause your computer to run slow
3.5. Some can re-install itself even after you think you have completely removed it
3.6. It can multiply
3.7. Much more easier to get it then to get rid of it
3.8. Just like a virus, in the sense that it infects your computer, but malware doesn't need you to "open it", it automatically does it.
4. How People Get Malware
4.1. Usually comes in a bundle with other programs
4.1.1. Such as Kaazaa, Imesh etc
4.1.2. Some pretend to be applications that you need to download first in order to view the website
4.1.3. Some can install themselves through holes on the Internet
4.1.3.1. When you enter the infected site, you get infected too
