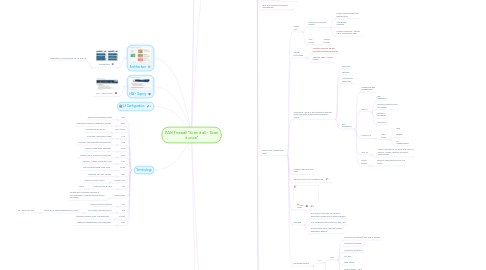
1. Architecture
1.1. Architecture
1.1.1. Dedicated Processing chip for NP and SP
2. HW - Osprey
2.1. HW - Osprey Venti
3. Any encrypted traffic that’s not being decrypted (SSL/SSH)
4. FW 1 Gbps
5. Administration Management
5.1. Account Administration
5.1.1. Scopes
5.1.1.1. Multiple admin
5.1.1.1.1. Logged in Configuration and System Log
5.1.1.2. External authentication
5.1.1.2.1. Local DB
5.1.1.2.2. Radius
5.1.1.2.3. AD
5.1.1.2.4. LDAP
5.1.1.2.5. Kerberos
5.1.1.2.6. User certificates
5.1.1.3. Abilities
5.1.1.3.1. Device level account
5.1.1.3.2. Virtual System level account
5.1.2. Server Profiles
5.1.2.1. Connection FW to the Servers that need to be contacted when authenticating the users
5.1.3. Authentication Profiles Sequences
5.1.3.1. Authentication Profiles
5.1.3.1.1. For account that is not local
5.1.3.2. Sequences
5.1.3.2.1. When there is multiple source of authentication
5.1.4. Web UI and XML Permissions
5.1.4.1. admin role
5.1.4.1.1. Web Gui
5.1.4.1.2. XML
5.1.4.1.3. CLI
5.1.5. CLI Permissions
5.1.5.1. superuser
5.1.5.2. superreader
5.1.5.3. deviceadmin
5.1.5.4. devicereader
5.2. Creating Administrator accounts
5.2.1. role
5.2.1.1. dynamic
5.2.1.1.1. user right defined in built in roles
5.2.1.2. role-based
5.2.1.2.1. user-defined role
5.2.2. Demo
5.2.2.1. Integrating with Radius
5.2.2.1.1. Server Profile
5.2.2.2. Authentication Sequence
5.2.2.2.1. Radius Server fail
5.3. Configuration Management
5.3.1. Configuration types
5.3.1.1. Candidate config
5.3.1.1.1. become running after commit
5.3.1.2. Running config
5.3.2. Commit operation
5.3.2.1. Granular config
5.3.2.1.1. Device and Network config
5.3.2.1.2. Object and Policy
5.3.2.2. Task
5.3.2.3. Validate
5.3.2.3.1. Save Version#, date/time
5.3.3. Transaction Lock
5.3.3.1. Config lock
5.3.3.1.1. block other user from making changes to the config
5.3.3.2. Commit Lock
5.3.3.2.1. block other admin from committing changes
5.3.4. Config Management
5.3.4.1. Demo
5.3.4.1.1. Device > Setup > Operations
5.3.5. Auditing
5.3.5.1. Demo
5.3.5.1.1. Device > Config Audit
5.3.6. Demo
5.3.6.1. Config Lock
5.3.6.2. Commit lock
5.4. PAN-OS Dynamic Updates
5.4.1. Licensing
5.4.1.1. Device > Support
5.4.1.2. Device > License
5.4.1.2.1. Threat Prevention
5.4.1.2.2. Decryption Port Mirroring
5.4.1.2.3. URL Filtering
5.4.1.2.4. Virtual System
5.4.1.2.5. Global Protect
5.4.1.2.6. WildFire
5.4.2. Dynamic Updates
5.4.2.1. Device > Dynamic Updates
5.4.2.1.1. anti virus signature
5.4.2.1.2. Applications
5.4.2.1.3. Application and Threat
5.4.2.1.4. url filtering db
5.4.2.1.5. Global protect Data
5.4.2.1.6. WildFire
5.4.3. Software Update
5.4.3.1. Device > Software
5.4.3.1.1. Base release must be downloaded .0 prior installing the maintenance release
5.4.3.2. Application and Threats dyn updates must be performed first to the recent package
5.4.3.3. updates.paloaltonetworks.com
5.4.4. Power Operations
5.4.4.1. Device > Setup > Operations
5.5. HSM
5.5.1. Hardware Security Module
5.5.1.1. SafeNet Luna SA
5.5.1.2. Thales Nshield Connect
5.6. Session Settings and Timeout
5.6.1. TCP init (5s)
5.6.1.1. Session timeout before SYN-ACK received
5.6.2. TCP half closed (120s)
5.6.2.1. Triggered 1st FIN
5.6.3. TCP time wait (15s)
5.6.3.1. Triggered 2nd FIN
5.6.3.1.1. value < TCP half closed
5.6.4. Global settings used by all apps
5.6.4.1. Timer settings at app level override global settings
5.6.5. Unverified RST
5.6.6. Config
5.6.6.1. Device > Setup > Sessions
5.6.6.2. show session info | match timeout
6. Interface Configuration
7. L3 Configuration
8. Platform and Architecture
8.1. PA-200 (Merlin)
8.1.1. Small and Medium Enterprise
8.1.1.1. FW throughput 100 Mbps, 1000 sessions per sec
8.1.1.1.1. Threat prevention 50 Mbps
8.1.1.2. 64000 max sessions
8.1.1.2.1. 1000 sessions per sec
8.1.1.3. 4 10/100/1000 Mbps interface
8.1.1.4. 25 IPSec VPN tunnels
8.1.1.4.1. 25 Global Protect
8.1.1.5. 10 Security Zones
8.1.1.6. 250 max number of policies
8.1.2. Architecture
8.1.2.1. Control Plane
8.1.2.1.1. Management
8.1.2.2. Data Plane
8.1.2.2.1. Signature Matching
8.1.2.2.2. Security Processing
8.1.2.2.3. Network Processing
8.1.2.2.4. Resources
8.1.3. HW
8.1.4. Differences
8.1.4.1. HA lite A/P
8.1.4.1.1. Use MGMT port as HA1
8.1.4.1.2. No HA2
8.1.4.2. no link aggregation
8.1.4.2.1. no vsys
8.2. PA-500 (Peregrine)
8.2.1. Medium-Enterprise networks
8.2.1.1. FW Throughput 250 Mbps
8.2.1.1.1. Threat Prevention 100 Mbps
8.2.1.2. 64000 max sessions
8.2.1.2.1. 7500 sessions per sec
8.2.1.3. (8) 10/100/1000 interfaces
8.2.1.4. 250 IPSec VPN tunnels
8.2.1.4.1. 100 GlobalProtect
8.2.1.5. 20 security zones
8.2.1.6. 1000 max number of policies
8.2.2. Medium to Large branch offices
8.2.3. Architecture
8.2.3.1. Control Plane
8.2.3.1.1. Configuration
8.2.3.1.2. Logging
8.2.3.1.3. Reporting
8.2.3.1.4. Resources
8.2.3.2. Data Plane
8.2.3.2.1. Signature Matching
8.2.3.2.2. Security Processing
8.2.3.2.3. Network processing
8.2.3.2.4. Resources
8.2.3.2.5. No FPGA chips
8.2.4. Specs
8.3. PA-2000 series (Kestrel)
8.3.1. PA-2020
8.3.1.1. Specifications
8.3.1.1.1. (12) 10/100/1000 interfaces, (2) Gigabit SFP
8.3.1.1.2. Throughput
8.3.1.1.3. 125000 max sessions
8.3.1.1.4. 1000 IPSec VPN tunnels
8.3.1.1.5. 1/6 virtual systems (base / max2)
8.3.1.1.6. 40 security zones
8.3.1.1.7. 2500 max number of polices
8.3.2. PA-2050
8.3.2.1. Specifications
8.3.2.1.1. (16) 10/100/1000 interfaces, (4) Gigabit SFP
8.3.2.1.2. Throughput
8.3.2.1.3. 250000 max sessions
8.3.2.1.4. 2000 IPSec VPN tunnels
8.3.2.1.5. 1/6 virtual systems (base/max)
8.3.2.1.6. 40 sec zones
8.3.2.1.7. 5000 max number of polices
8.3.3. High Speed Networks of Medium to Large branch
8.3.4. Going to EOS
8.3.4.1. 30 April 2015
8.3.5. HW
8.4. PA-3000 series
8.4.1. 3060
8.4.1.1. Front to back airflow
8.4.1.2. Redundant power supply
8.4.1.3. 2x 10G SFP
8.4.2. Specs
8.5. PA-4000 series (Falcon)
8.5.1. EOS
8.5.2. Specs
8.6. PA-5000 series (Hawk)
8.6.1. HW
8.6.2. Switch Fabric 80Gbps
8.6.2.1. QoS 20Gbps
8.6.3. Specs
8.6.3.1. Architecture
8.6.3.1.1. 5060
8.7. PA-7050 (Condor)
8.7.1. HW
8.8. PA-7080
8.8.1. HW
8.9. Performance
8.9.1. Intranet
8.10. Next Gen Appliances Malware Management
8.10.1. WildFire
8.10.1.1. WF-500
8.10.1.1.1. org prefer not to use public cloud
8.10.1.1.2. identify, analise, blocks unknown malware
8.10.1.2. Public Cloud Service
8.10.2. Panorama
8.10.2.1. M-100
8.10.2.1.1. Centralized management and logging functions
8.10.2.2. Virtual Panorama
8.10.3. Virtualized Firewalls
8.10.3.1. Gateway
8.10.3.1.1. VM-100
8.10.3.1.2. VM-200
8.10.3.1.3. VM-300
8.10.3.1.4. VM-1000-HC
8.10.3.2. VM-1000-HV
8.10.3.2.1. For NSX
8.10.4. GP100
8.10.4.1. Mobile Security Management
8.11. Single-Pass Architecture (SP3)
8.11.1. Single Pass
8.11.1.1. Operations once per packet
8.11.1.1.1. Traffic Classification (app Identification
8.11.1.1.2. User/group mapping
8.11.1.1.3. Content scanning - threats, URLs, confidential data
8.11.1.2. One policy
8.11.1.2.1. Stream based
8.11.2. Parallel Processing
8.11.2.1. Function-specific parallel processing hardware engines
8.11.2.2. Separate data / control planes
8.11.3. SP3 Engine : each of the protection features utilize the same stream-based signature format
8.11.3.1. AntiVirus
8.11.3.2. Spyware
8.11.3.3. Vulnerability Protection
8.11.3.4. Key processing
8.11.3.4.1. Networking and management
8.11.3.4.2. App-ID
8.11.3.4.3. Content-ID
8.11.3.4.4. User-ID
8.11.3.4.5. Policy Engine
8.11.4. Control Plane and Data Plane
8.11.5. The Evolution of SP3 Architecture
8.11.6. Flow Logic
8.11.7. FastPath
8.11.7.1. Any traffic that does not perform application-shifts and no known threats
8.11.7.2. Any network protocols (OSPF, BGP, RIP)
8.11.7.3. During Application Override (bypass application engine)
8.11.8. Discarded packet
8.11.8.1. L3
8.11.8.1.1. IPv4
8.11.8.1.2. IPv6
8.11.8.2. L4
8.12. Initial Config
8.12.1. MGMT IP : 192.168.1.1
8.12.1.1. username/password : admin/admin
8.12.2. CLI
8.12.2.1. Configuration Mode #
8.12.2.1.1. set deviceconfig system
8.12.2.1.2. show job processed
8.12.2.2. Operation Mode >
8.12.2.2.1. configure
8.13. GUI Interface
8.13.1. Navigation
8.13.1.1. Monitoring Function
8.13.1.1.1. Dashboard
8.13.1.1.2. ACC
8.13.1.1.3. Monitor
8.13.1.2. Configuration
8.13.1.2.1. Policies
8.13.1.2.2. Objects
8.13.1.2.3. Network
8.13.1.2.4. Device
8.13.1.3. Task
8.13.1.4. Help
8.13.1.4.1. Administration Guide
8.13.1.5. Language
8.13.1.6. GUI errors
8.13.1.6.1. Red
8.13.1.6.2. Yellow highlights
8.14. CLI
8.14.1. Modes
8.14.1.1. Operation
8.14.1.1.1. Execute immediately
8.14.1.2. Configuration
8.14.1.2.1. Changes will be stored in memory until committed
8.14.2. Tools
8.14.2.1. pipe |
8.14.2.1.1. match
8.14.2.1.2. except
8.14.3. Find
8.14.3.1. find command keyword "vpn"
8.14.4. Debugs
8.14.4.1. debug management-server on debug
8.14.5. Logs
8.15. API
8.15.1. allow external system to execute command remotely to PAN FW or Panorama server
8.15.2. https://hostname/api
8.15.2.1. rest API browser
8.15.3. Demo
8.15.3.1. Change dns-server Device > Service
8.15.3.1.1. Commit via XML API
9. Terminology
9.1. APT
9.1.1. Advanced Persistent Threat
9.2. ASIC
9.2.1. Application Specific Integrated Circuits
9.3. C&C Server
9.3.1. Command and Control
9.4. CIM
9.4.1. Common Information Model
9.5. CVE
9.5.1. Common Vulnerabilities and Exposure
9.6. DGA
9.6.1. Domain Generation Algorithm
9.7. DSRI
9.7.1. Disable Server Response Inspection
9.8. EC2
9.8.1. Amazon - Elastic Compute Cloud
9.9. FPGA
9.9.1. Field Programmable Gate Array
9.10. HSM
9.10.1. Hardware Security Module
9.11. Juniper UAC
9.11.1. Unified Access Control
9.12. LPC
9.12.1. Log Processing Card
9.12.1.1. 7050
9.13. Obfuscation
9.13.1. the hiding of intended meaning in communication, making communication confusing
9.14. PFS
9.14.1. Perfect Forward Secrecy
9.15. SSD
9.15.1. Solid State Storage Device
9.15.1.1. introduce in new architecture PA-5000
9.15.1.1.1. PA-4000 has HDD
9.16. SLAAC
9.16.1. Stateless Address Auto-Configuration
9.17. WMI
9.17.1. Windows Management Instrumentation

