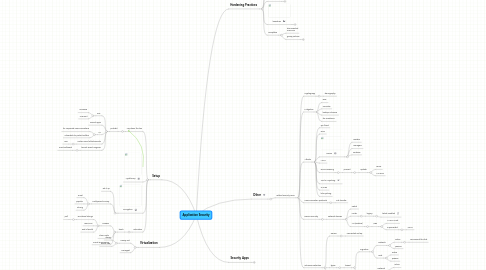
1. Setup
1.1. Lay down the law
1.1.1. prohibit
1.1.1.1. P2P
1.1.1.1.1. Limewire
1.1.1.1.2. UTorrent
1.1.1.2. Torrent apps
1.1.1.3. IM
1.1.1.3.1. for corporate communications
1.1.1.3.2. vulnerable to packet sniffers
1.1.1.4. certain email attachements
1.1.1.4.1. .exe
1.1.1.5. torrent search engines
1.1.1.5.1. most outlawed
1.2. Wyatt Earp
1.3. encryption
1.3.1. set it up
1.3.2. PrettyGood Privacy
1.3.2.1. email
1.3.2.2. popular
1.3.2.3. strong
1.4. education
1.4.1. teach
1.4.1.1. Hoaxes
1.4.1.1.1. emotional strings
1.4.1.1.2. new virus
1.4.1.1.3. end of world
1.4.1.2. chain mails
1.4.1.3. social engineering
2. Virtualization
2.1. Honey Pot
2.1.1. decoy
2.1.2. virtual SQL
2.2. Honeypot
3. Hardening Practices
3.1. updates
3.1.1. Auto
3.1.1.1. pros
3.1.1.1.1. set it and forget it
3.1.1.2. cons
3.1.1.2.1. latest update conflicts with other apps
3.1.2. Workstation update managment
3.1.2.1. WSUS
3.1.3. track changes
3.1.3.1. keep a log
3.1.3.1.1. hard log reccomended
3.1.3.2. software
3.1.3.2.1. 3rd party packages exist
3.1.3.2.2. WSUS
3.1.3.3. be a team player
3.1.3.3.1. keep comm
3.1.3.3.2. people move on
3.2. OS/NOS
3.2.1. removal
3.2.1.1. unnessesary
3.2.1.1.1. software
3.2.1.1.2. options
3.2.1.1.3. services
3.2.1.1.4. Examples
3.2.2. existing/needed services
3.2.2.1. configure properly
3.2.2.1.1. Examples
3.2.2.1.2. File safegaurds
3.2.3. Server
3.2.3.1. system files
3.2.3.1.1. files should be stored on a separate disk or partition to ensure these system files are not accidentally accessed or removed
3.2.3.2. Do
3.2.3.2.1. apply
3.2.3.2.2. check vender website frequently for news and updates
3.2.3.2.3. secure behind locked door
3.2.3.2.4. install HIDS
3.2.3.3. Don't
3.2.3.3.1. Surf Web
3.2.3.3.2. install software from fly by night company
3.2.3.3.3. install patch
3.2.3.4. Server admins
3.2.3.4.1. activate security options
3.2.3.4.2. Know
3.2.3.4.3. Logs
3.2.3.4.4. ACL
3.2.3.4.5. harden your system
3.2.3.4.6. Know thyself do you
3.2.3.4.7. Be very familiar with different types of security vulnerabilities inherent with each type of Internet server and know how to prevent them from being exploited.
3.2.3.4.8. balance
3.3. Good Practice
3.3.1. start with nothing and add as needed
3.3.1.1. not the other way around
3.3.1.2. least privledge
3.4. baselines
3.4.1. history of past security vulnerabilities
3.4.1.1. compile
3.4.1.2. time intensive
3.4.1.2.1. length
3.4.1.2.2. 2-3 weeks minimum
3.4.1.2.3. nights and weekends
3.4.2. industry security standards
3.4.3. info gather
3.4.3.1. organizations
3.4.3.2. associations
3.4.3.3. other admins
3.4.3.3.1. don't be shy talk!
3.4.4. Tools
3.4.4.1. MicroSoft
3.4.4.1.1. Microsoft Baseline Security Analyzer (MBSA)
3.5. Templates
3.5.1. documented minimum
3.5.2. group policies
3.5.2.1. accounting
3.5.2.1.1. financial data
3.5.2.1.2. salaries
3.5.2.2. marketing
3.5.2.3. Sales
3.5.2.3.1. pricing
3.5.2.4. HR
3.5.2.4.1. confidential data
3.5.2.5. each grop policy uniqe based on role
3.5.2.6. be mindful that if employee moves to a diff dept rights must be added/taken away
3.5.2.7. Role based access control
3.5.2.7.1. most popular
3.5.2.7.2. highly customizeble
3.5.2.7.3. fairly secure
3.5.2.7.4. centraly administered
4. Security Apps
4.1. Personal Firewalls
4.1.1. Windows firewall
4.1.1.1. heavily critized
4.1.1.2. too integrated with OS I think
4.1.1.2.1. other examples of app heavily integrated into OS
4.1.2. Symantec
4.1.3. Mcafee
4.2. Antivirus
4.2.1. versions
4.2.1.1. email
4.2.1.2. regular
4.2.2. parts
4.2.2.1. engine
4.2.2.1.1. stays the same
4.2.2.2. signature files
4.2.2.2.1. viruses contain or create a specific binary code detectable by the signature file
4.2.2.2.2. engineers make the signature files
4.2.3. Price
4.2.3.1. about $40
4.2.3.2. military next to nothing or free
4.3. Caution!
4.3.1. if when installing an app and the install program prompts you to turn of your AV be weary!
4.3.2. If you turn off AV in order to install a program or to make some change remember to turn it back on!
5. Other
5.1. related security issue
5.1.1. cryptograpy
5.1.1.1. stenography
5.1.2. Mitigation
5.1.2.1. DRP
5.1.2.2. OFFsites
5.1.2.3. backup schemes
5.1.2.4. fire resistance
5.1.3. Attacks
5.1.3.1. syn flood
5.1.3.2. DOS
5.1.3.3. DDOS
5.1.3.3.1. masters
5.1.3.3.2. managers
5.1.3.3.3. zombies
5.1.3.4. MITM
5.1.3.5. DNS Poisening
5.1.3.5.1. prevent
5.1.3.6. TCP/IP Hijacking
5.1.3.7. SMURF
5.1.3.8. blue jacking
5.1.4. Communication protocols
5.1.4.1. File transfer
5.1.5. Device Security
5.1.5.1. network devices
5.1.5.1.1. switch
5.1.5.1.2. router
5.1.5.1.3. AP (wireless)
5.1.6. Intrusion Detection
5.1.6.1. Sensor
5.1.6.1.1. connected via tap
5.1.6.2. types
5.1.6.2.1. based
5.1.6.3. venders
5.1.6.3.1. Norton
