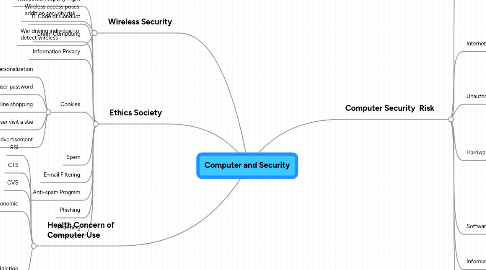
1. Wireless Security
1.1. Wireless access poses addition security risk
1.2. War driving individual to detect wireless
2. Health Concern of Computer Use
2.1. RSI
2.2. CTS
2.3. CVS
2.4. Ergonomic
2.4.1. Applied science devote to incoroperating comfort
2.5. Computer Addiction
2.5.1. Crave computer time
2.5.2. Overjoin when at the computer
2.5.3. Unable stopped computer activities
2.5.4. Irritable when not at the computer
2.5.5. Neglect family and friend
2.5.6. Peoblem at work or school
3. Ethics Society
3.1. Intellectual Property Right
3.2. IT Code of Conduct
3.3. Green Computing
3.4. Information Privacy
3.5. Cookies
3.5.1. Allow for personalization
3.5.2. Storage user password
3.5.3. Assist with online shopping
3.5.4. Track how often user visit a stie
3.5.5. Target advertisement
3.6. Spam
3.7. E-mail Filtering
3.8. Anti-spam Program
3.9. Phishing
3.10. Pharming
4. Computer Security Risk
4.1. Cybercrime
4.1.1. Hackers
4.1.2. Crackers
4.1.3. Script Kiddies
4.1.4. Corporate Spies
4.1.5. Unethical Employee
4.1.6. Cyberextortionists
4.1.7. Cyberterrorists
4.2. Internet and Network Attacks
4.2.1. Online Security Service
4.2.2. Computer Virus
4.2.3. Worm
4.2.4. Trojan Horse
4.2.5. Rootkit
4.3. Unauthorize and Access User
4.3.1. Digital Forensics
4.4. Hardware Theft
4.4.1. Physical Access Control
4.4.2. Alarm System
4.4.3. Cable to Lock Equipment
4.4.4. Realtime Location System
4.4.5. Password,Possessed,Objectives and Biometric
4.5. Software Theft
4.5.1. Steal Software Media
4.5.2. Intentionally Eares Program
4.5.3. Illegal Copies a Programs
4.6. Information Theft
4.6.1. Encryption
4.7. System Failure
4.7.1. Aging Hardware
4.7.2. Natural Disaster
4.7.3. Electrical Power Problem
4.7.4. Error in Computer Programs
