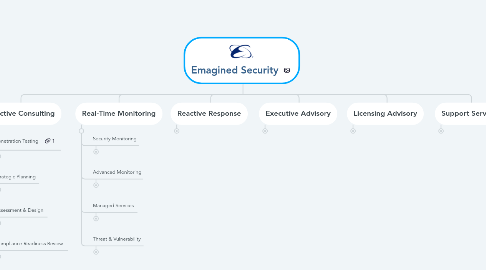
1. Proactive Consulting
1.1. Penetration Testing
1.1.1. Red Team Testing
1.1.2. Internal Network
1.1.3. External Network
1.1.4. Web Application
1.1.5. Social Engineering
1.1.6. Wireless
1.1.7. IOT
1.1.8. Cloud
1.1.9. Virtualized
1.1.10. Custom
1.2. Strategic Planning
1.2.1. Policies, Procedures, Standards & Guidelines
1.2.2. Governance Frameworks
1.2.3. Business Continuity
1.2.4. Disaster Recovery
1.3. Assessment & Design
1.3.1. Budget Creation Workshops
1.3.2. Security Risk & Maturity
1.3.3. Security Architecture
1.3.4. Virtual Environment
1.3.5. Network Segmentation
1.3.6. Thrid Party Vendors
1.3.7. Mergers & Acquisitions
1.3.8. Security Technology
1.3.9. Compliance Readiness
1.3.10. Configuration Reviews
1.4. Compliance Readiness Review
1.4.1. IS 27001-2
1.4.2. NIST
1.4.3. RMF
1.4.4. NISPOM
1.4.5. DFARS
1.4.6. PCI
1.4.7. HIPAA
1.4.8. GDPR
1.4.9. FedRamp
1.4.10. FISMA
1.4.11. SCADA
1.4.12. NERC/FERC
2. Real-Time Monitoring
2.1. Security Monitoring
2.1.1. Security Log Collection
2.1.2. Forensic Log Analysis
2.1.3. Data Incident Correlation
2.1.4. Alert Generation
2.1.5. Incident Prioritization
2.2. Advanced Monitoring
2.2.1. Indicators of Compromise
2.2.2. Homoglyph Domain Alerting
2.2.3. Suspicious User Detection
2.2.4. Domain Generation Algorithm (DGA) Detection
2.2.5. Suspicious VPN Monitoring
2.2.6. Public Credential Exposures
2.2.7. Rogue Device Detection
2.2.8. Slack / HipChat Alerting
2.3. Managed Services
2.3.1. Perimeter (FW / VPN / IDS / IPS)
2.3.2. APT Technology
2.3.3. Encryption / PKI / HSMs
2.3.4. Spam & Messaging
2.3.5. Data Loss Prevention
2.3.6. End Point Protection
2.4. Threat & Vulnerability
2.4.1. Vulnerability Reporting
2.4.2. Intelligence
2.4.3. Threat Warning
2.4.4. Asset Tracking
3. Reactive Response
3.1. INCIDENT RESPONSE
3.1.1. IR Planning & Development
3.1.2. Incident Management
3.1.3. Incident Responders
3.1.4. Retained or OnDemand Support
3.2. INCIDENT ANALYSIS
3.2.1. Data Capture
3.2.2. Digital Forensics
3.2.3. Malware & Ransomware Recovery
3.2.4. Cyber Stalking
3.2.5. Reverse Engineering
3.2.6. Evidence Discovery
3.2.7. Incident Reporting
3.2.8. Evidence Custodianship
3.3. CYBER & SECURITY LITIGATION SUPPORT
3.3.1. e-Discovery
3.3.2. Legal Action Preparation, Response & Analysis
3.3.3. Expert Witnesses
4. Executive Advisory
4.1. CISO ON-DEMAND
4.1.1. Interim or Virtual CISO
4.1.2. Program Development
4.1.3. Program Management
4.1.4. Budget Planning
4.1.5. Resource Planning
4.1.6. Secure Business Solutions
4.2. CORPORATE STRATEGY
4.2.1. Healthcheck & Prioritization
4.2.2. Executive Security Briefings
4.2.3. Initiative Prioritization
4.2.4. Vendor Analysis
4.2.5. Security Portfolio Analysis
4.3. COST REDUCTION & CONSOLIDATION
4.3.1. Budgetary Analysis
4.3.2. Cloud Adoption
4.3.3. Virtualization Options
4.3.4. Outsourcing Feasibility
4.3.5. Licensing Evaluation
4.4. EXECUTIVE AUDIT SERVICES
4.4.1. Management
4.4.2. Preparation
4.4.3. Impact Reduction
4.4.4. Finding Disputes
4.4.5. Sensitivity Training
4.5. SECURITY EDUCATION
5. Licensing Advisory
5.1. SOLUTION ANALYSIS
5.1.1. Buy vs Build Analysis
5.1.2. Requirements Gathering Requirements Analysis & Documentation
5.2. SOLUTION VALIDATION
5.2.1. Solution Evaluation & Recommendation
5.2.2. Laboratory Testing
5.2.3. Solution Documentation
5.2.4. Vulnerability Testing
5.2.5. Implementation & Rollout
5.3. LICENSING SERVICES
5.3.1. Licensing Support
5.3.2. Cost Analysis
5.3.3. Vendor Liaison
5.3.4. Vendor Negotiations
5.3.5. Price Negotiations
6. Support Services
6.1. PROJECT MANAGEMENT
6.1.1. Security Projects
6.1.2. Solution Implementations
6.1.3. Security Programs
6.2. RESOURCE AUGMENTATION
6.2.1. Senior Security Management
6.2.2. Security Engineers
6.3. IMPLEMENTATION SERVICES
6.3.1. Security Technologies
6.3.2. (eg, PKI, HSM, FW)
6.3.3. Installations & Migrations Privacy & Compliance
6.3.4. Asset Management
6.3.5. Security SDLC
6.3.6. ITIL Service Lifecycle
6.3.7. Custom Implementations
6.4. ANALYTICS
6.4.1. Executive Reporting
6.4.2. Data Correlation
6.4.3. Data Analysis & Reporting
6.4.4. Metrics Development & Implementation
