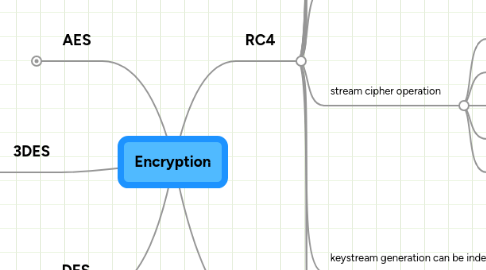
1. DES
1.1. Data Encryption Standard
1.2. 56-bit
1.3. modified version of IBMs Lucifer algorithm (128-bit)
1.4. adopted by NIST as federal standard November 23, 1976
1.5. specification published in January 1977
1.6. quickly became widely-employed
1.7. find DES key by brute force
1.7.1. various shortcut attacks found
1.7.2. computers speed
1.8. encrypts and decrypts in 64-bit blocks
1.8.1. every 8th bit used for parity
1.8.2. effective key strength = 56 bits
1.8.3. takes 64-bit plaintext block as input
1.8.4. outputs 64-bit ciphertext block
1.8.5. has 16 rounds
1.8.6. # rounds exponentially proportional to time required to crack
1.9. 56-bit not appropriate for high security apps
1.10. abandoned by NIST in 1997
1.11. began work on replacement - AES
1.12. still widely used
2. 3DES
2.1. DES developed by IBM around 1974
2.2. adopted as national standard in 1977
2.3. 3DES minor variation of this
2.4. 3 times slower than DES
2.5. far more secure than DES
2.6. 3 64-bit keys = 192 bit overall length
2.7. same procedure as DES but repeated 3 times
2.8. procedure
2.8.1. Start with plaintext block
2.8.2. Encrypt with Key 1
2.8.3. Decrypt with Key 2
2.8.4. Encrypt with Key 3
2.8.5. Output Ciphertext block
2.8.6. Decrypt in reverse
2.9. All Keys should be different
2.10. 8 parity bits for each key = 168 bit effective strength
3. AES
3.1. Advanced Encryption Standard
3.2. NIST initiated selection in 1997
3.3. symmetric-key encryption
3.4. for unclassified Federal information
3.5. initial candidates
3.5.1. MARS
3.5.2. RC6
3.5.3. Rijndael
3.5.4. Serpent
3.5.5. Twofish
3.6. Selected Rijndael "Rhine-Dahl"
3.7. intended to be several orders of magnitude more secure than DES only marginally slower
3.8. expected to have a life of 20-30 years
3.9. will require new APs and wireless NICs
3.10. CPU intensive
3.11. included in IEEE 802.11i draft
3.12. capable of 128, 192 and 256-bit keys
3.13. considered uncrackable
4. RC4
4.1. Ron Rivest
4.2. RSA Security
4.3. variable length stream cipher
4.4. fast
4.5. efficient
4.6. most common stream cipher used today
4.7. used in:
4.7.1. WEP
4.7.2. TKIP
4.7.3. SSL
4.7.4. TLS
4.7.5. MPPE
4.7.6. many others
4.8. symmetric encryption algorithm
4.9. operate on smaller units of plaintext (bits)
4.10. much faster than block ciphers
4.10.1. operate on large blocks of data
4.10.2. slow
4.11. stream cipher operation
4.11.1. operate on smaller units of plaintext (usually bits)
4.11.2. generates a keystream
4.11.3. sequence of bits used as a key
4.11.4. combine keystream with plaintext
4.11.5. bitwise XOR operation
4.12. keystream generation can be independent of:
4.12.1. plaintext
4.12.2. ciphertext
4.12.3. yields synchronous stream cipher
4.12.4. otherwise called self-synchronizing
4.12.4.1. depend on
4.12.4.1.1. data
4.12.4.1.2. encryption
4.13. capable of key lengths
4.13.1. up to 256 bits
4.13.2. typically
4.13.2.1. 64 bits
4.13.2.2. 128 bits
4.13.2.3. 256 bits
4.14. considered moderately secure
4.14.1. WEP has been broken!
4.14.2. WEP is weak, not RC4
4.14.3. TKIP
4.14.3.1. fixes problems with WEP
4.14.3.2. still uses RC4
5. RC5
5.1. Ron Rivest
5.2. RSA Security
5.3. developed in 1994
5.4. block cipher
5.4.1. fastest
5.4.2. most well-known
5.5. developed for use in software
5.6. extremely efficient on "fast" processors (Pentium and above)
5.7. parameterized algorithm
5.8. variable
5.8.1. block size
5.8.1.1. 32 bits (experimentation/evaluation)
5.8.1.2. 64 bits (drop-in replacement for DES)
5.8.1.3. 128 bits
5.8.2. key size (0 to 2040 bits)
5.8.3. number of rounds (0 to 255)
5.9. 3 routines
5.9.1. key expansion
5.9.1.1. user-provided secret key
5.9.1.2. expanded to fill key table
5.9.1.3. size depends on number of rounds
5.9.1.4. key table used for encryption/decryption
5.9.2. encryption
5.9.2.1. integer addition
5.9.2.2. bitwise XOR
5.9.2.3. variable rotation
5.9.3. decryption
5.10. exceptionally simple
5.11. easy to implement and analyze
5.12. July 14, 2002
5.12.1. Distributed.Net
5.12.2. broke 64-bit RC5 key
5.12.3. 1757 days of computation
5.12.4. ~ 59 billion keys tested
5.12.5. peak rate 270 million keys per second
5.13. December 3, 2002
5.13.1. project to break 72-bit RC5
