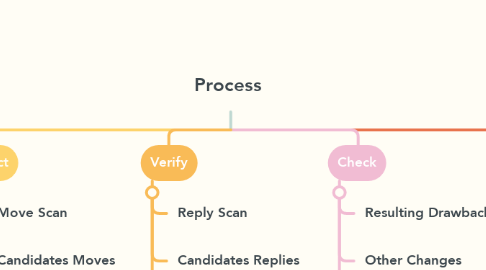
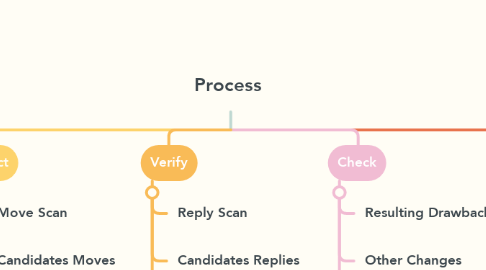
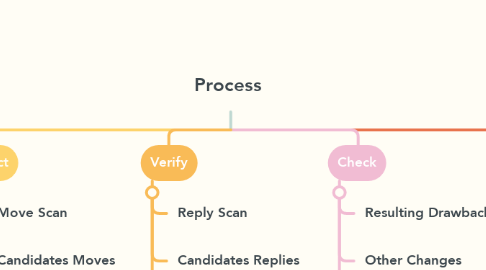
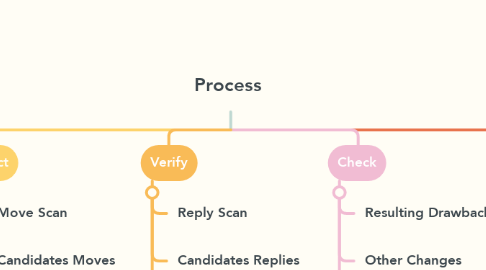
Process
作者:adel alizadeh
1. Update
1.1. Created Threats
1.2. Resulting Drawbacks
1.3. Other Changes
2. Select
2.1. Move Scan
2.2. Candidates Moves
2.3. Move Selection
3. Verify
3.1. Reply Scan
3.2. Candidates Replies
3.3. Reply Evaluation
4. Check
4.1. Resulting Drawbacks
4.2. Other Changes
4.3. Overlooked Replies
5. Execute
5.1. Move
5.2. Clock
5.3. Notate
6. Prepare
6.1. Prophylaxis
6.2. Objectives
6.3. Plan