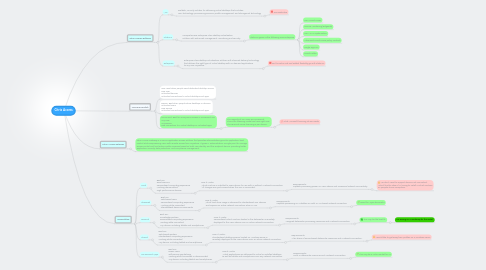
1. XenDesktop
1.1. Local
1.1.1. Best For: Road warriors Personalized computing experience Working disconnected High-performance devices
1.1.1.1. How it Works: Virtual machine is installed to users device for use with or without a network connection. All changes are synchronized when the user is connected.
1.1.1.1.1. Requirements: Capable processing power on users device and occasional network connectivity.
1.2. Streamed
1.2.1. Best For: Task-based users Personalized computing experience Working while connected Standardized device environments
1.2.1.1. How it Works: Virtual hard drive image is streamed to standardized user devices and requires an active network connection when in use.
1.2.1.1.1. Requirements: Capable processing on a diskless PC with a LAN-based network connection
1.3. Personal
1.3.1. Best For: Knowledge workers Personalized computing experience Working while connected Any device, including tablets and smartphones
1.3.1.1. How it Works: Personalized virtual machine hosted in the datacenter is remotely displayed to the users device over an active network connection.
1.3.1.1.1. Requirements: Assigned datacenter processing resources and a network connection.
1.4. Shared
1.4.1. Best For: Task-based workers Standardized computing experience Working while connected Any device, including tablets and smartphones
1.4.1.1. How it Works: Standardized desktop session hosted on Windows server is remotely displayed to the users device over an active network connection.
1.4.1.1.1. Requirements: A fair share of server-based datacenter resources and a network connection.
1.5. On-Demand Apps
1.5.1. Best For: Power users Self-service app delivery Working while connected or disconnected Any device, including tablets and smartphones
1.5.1.1. How it Works: Virtual applications are delivered to virtual or installed desktops as well as tablets and smartphones over any network connection.
1.5.1.1.1. Requirements: Local or datacenter resources and a network connection.
2. Licensing Models
2.1. User: Best when people need dedicated desktop access. One User Unlimited devices Unlimited connections to virtual desktops and apps
2.2. Device: Best when people share desktops or devices. Unlimited Users One Device Unlimited connections to virtual desktops and apps
2.3. Concurrent: Best for anonymous access or occasional use. Any User Any Device One connection to a virtual desktop or unlimited apps
2.3.1. The majority of our users are occasional. This is the licensing model we have right now. The Terminal Server licensing is per device.
2.3.1.1. What Microsoft licensing do we need?
3. Citrix License Editions
3.1. VDI
3.1.1. Scalable VDI-only solution for delivering virtual desktops that includes: HDX technology, provisioning services, profile management, and StorageLink technology
3.1.1.1. Too Restrictive
3.2. Platinum
3.2.1. Comprehensive enterprise-class desktop virtualization solution with advanced management, monitoring and security.
3.2.1.1. Platinum gives us the following over Enterprise
3.2.1.1.1. HDX SmartAccess
3.2.1.1.2. Service Monitoring (EdgeSite)
3.2.1.1.3. HDX WAN Optimization
3.2.1.1.4. Advanced SmartAccess policy controls
3.2.1.1.5. Single Sign-On
3.2.1.1.6. SmartAuditor
3.3. Enterprise
3.3.1. Enterprise-class desktop virtualization solution with FlexCast delivery technology that delivers the right type of virtual desktop with on-demand applications to any user, anywhere.
3.3.1.1. For the extra cost and added flexibility go with Platinum
