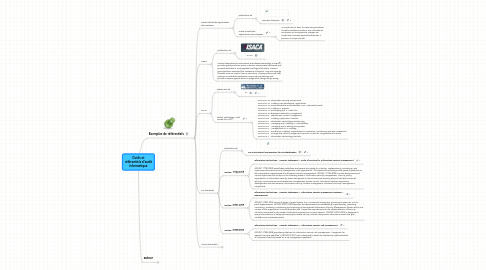
1. Exemples de référentiels
1.1. Guide d'audit des applications informatiques
1.1.1. publication de
1.1.1.1. Chambre fiduciaire
1.1.2. Guide d'audit des applications informatiques
1.1.2.1. Le Guide décrit, dans le cadre des procédures d’audit orientées processus, une méthode de vérification et une approche intégrée de l’audit des contrôles applicatifs destinées à prévenir ce risque d’audit.
1.2. COBIT
1.2.1. publication de
1.2.1.1. ISACA
1.2.2. Control Objectives for Information and related Technology (COBIT®) provides good practices across a domain and process framework and presents activities in a manageable and logical structure. COBIT’s good practices represent the consensus of experts. They are strongly focused more on control, less on execution. These practices will help optimise IT-enabled investments, ensure service delivery and provide a easure against which to judge when things do go wrong.
1.3. GTAG
1.3.1. publication de
1.3.1.1. IIA
1.3.2. Global Technology Audit Guides (GTAG®)
1.3.2.1. PG GTAG-15: Information Security Governance PG GTAG-14: Auditing User-developed Applications PG GTAG-13: Fraud Prevention and Detection in an Automated World PG GTAG-12: Auditing IT Projects PG GTAG-11: Developing the IT Audit Plan PG GTAG-10: Business Continuity Management PG GTAG-9: Identity and Access Management PG GTAG-8: Auditing Application Controls PG GTAG-7: Information Technology Outsourcing PG GTAG-6: Managing and Auditing IT Vulnerabilities PG GTAG-5: Managing and Auditing Privacy Risks PG GTAG-4: Management of IT Auditing PG GTAG-3: Continuous Auditing: Implications for Assurance, Monitoring, and Risk Assessment PG GTAG-2: Change and Patch Management Controls: Critical for Organizational Success PG GTAG-1: Information Technology Controls
1.4. ISO standards
1.4.1. publication de
1.4.1.1. ISO International Organization for Standardization
1.4.2. ISO/IEC 17799:2005
1.4.2.1. Information technology -- Security techniques -- Code of practice for information security management
1.4.2.2. ISO/IEC 17799:2005 establishes guidelines and general principles for initiating, implementing, maintaining, and improving information security management in an organization. The objectives outlined provide general guidance on the commonly accepted goals of information security management. ISO/IEC 17799:2005 contains best practices of control objectives and controls in the following areas of information security management: security policy; organization of information security; asset management; human resources security; physical and environmental security; communications and operations management; access control; information systems acquisition, development and maintenance; information security incident management; business continuity management; compliance.
1.4.3. ISO/IEC 27001:2005
1.4.3.1. Information technology -- Security techniques -- Information security management systems -- Requirements
1.4.3.2. ISO/IEC 27001:2005 covers all types of organizations (e.g. commercial enterprises, government agencies, not-for profit organizations). ISO/IEC 27001:2005 specifies the requirements for establishing, implementing, operating, monitoring, reviewing, maintaining and improving a documented Information Security Management System within the context of the organization's overall business risks. It specifies requirements for the implementation of security controls customized to the needs of individual organizations or parts thereof. ISO/IEC 27001:2005 is designed to ensure the selection of adequate and proportionate security controls that protect information assets and give confidence to interested parties.
1.4.4. ISO/IEC 27005:2008
1.4.4.1. Information technology -- Security techniques -- Information security risk management
1.4.4.2. ISO/IEC 27005:2008 provides guidelines for information security risk management. It supports the general concepts specified in ISO/IEC 27001 and is designed to assist the satisfactory implementation of information security based on a risk management approach.
1.5. Autres référentiels
1.5.1. OECD recommendations
1.5.1.1. The OECD Working Party on Information Security and Privacy (WPISP) (overview of its work) develops policy options to sustain trust in the Internet Economy, working in areas such as: Critical Information Infrastructure (CII), Digital Identity Management (IDM) and e-authentication, Malware, Radio-Frequency Identification (RFID) and sensor networks, The OECD Privacy Guidelines, Protecting children online, Privacy law enforcement co-operation
1.5.2. Outsourcing
1.5.2.1. SAS 70
1.5.2.1.1. publication de
1.5.2.1.2. Statement on Auditing Standards No. 70 (SAS 70) provides guidance to service auditors when assessing the internal controls of a service organization and issuing a service auditor’s report.
1.5.2.2. ISAE 3402
1.5.2.2.1. publication de
1.5.2.2.2. International standard on assurance engagement (ISAE) 3402 - Assurance reports on controls at a service organisation
1.5.3. OWASP
1.5.3.1. The Open Web Application Security Project (OWASP) is a not-for-profit worldwide charitable organization focused on improving the security of application software. Our mission is to make application security visible, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license
1.5.4. ...
2. auteur
2.1. Marc Barbezat
2.1.1. sur b3b
2.1.2. sur LinkedIn
