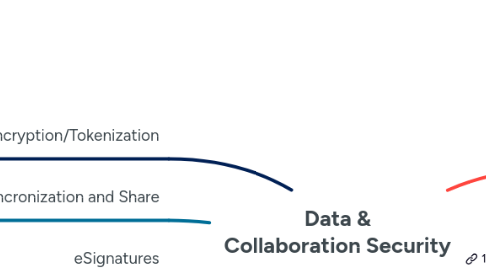
1. Encryption/Tokenization
1.1. Big Data
1.1.1. Gazzang
1.1.2. Vormetric
1.2. Cloud/SAAS Encryption
1.2.1. Appliances
1.2.1.1. Office365
1.2.1.1.1. Vaultive
1.2.1.1.2. FiLink
1.2.1.2. Ciphercloud
1.2.1.3. Afore Solutions
1.2.1.3.1. CloudLink VSA
1.2.1.4. Perspecsys
1.2.2. Software
1.2.2.1. BoxCryptor
1.2.2.2. CloudMask
1.2.2.3. PrivateCore
1.2.2.4. Trend Micro
1.2.2.4.1. SecureCloud
1.2.2.5. Viivo
1.2.2.6. Voltage Security
1.2.3. Software as a Service
1.2.3.1. Trend Micro
1.2.3.1.1. SecureCloud
1.2.3.2. SooKasa
1.2.3.3. Thales
1.2.3.3.1. SafeMonk
1.3. Cryptographic Providers
1.3.1. RSA
1.3.2. Quintessence
1.3.3. Microsoft
1.4. Data masking
1.4.1. Oracle
1.4.2. Dataguise
1.4.3. Informatica
1.4.4. IBM
1.4.5. Voltage Security
1.4.6. Green SQL
1.4.7. Mentis
1.4.8. Compuware
1.4.9. Axis
1.4.10. Privacy Analytics
1.4.11. Camouflage Software
1.4.12. Solix Technologies
1.4.13. Net 2000
1.5. Database
1.5.1. Thales
1.5.2. Dark Matter Labs
1.5.3. Vormetric
1.6. Email
1.6.1. ZixCorp
1.6.2. Encryptics
1.6.2.1. https://www.encryptics.com/default.aspx
1.7. Encrypted USB Storage
1.7.1. Apricorn
1.7.2. Datalocker
1.7.3. EgoSecure
1.7.4. Integral Memory
1.7.5. IronKey
1.7.6. Kingston
1.7.7. Virbatim
1.8. File/Folder
1.8.1. Covertix
1.8.1.1. http://www.covertix.com/
1.8.2. EgoSecure
1.8.3. IBM
1.8.3.1. Mainframe
1.8.3.1.1. z10
1.8.4. SecureIslands
1.8.5. Sophos
1.8.5.1. SafeGuard Enterprise (Utimaco)
1.8.6. Symantec (PGP)
1.8.7. Vormetric
1.8.8. WinMagic
1.8.8.1. SecureDoc
1.9. Quantum Encryption
1.9.1. IDQ
1.9.2. Quintessence Labs
1.9.3. Whitewood Encryption
1.10. Tokenization
1.10.1. Altr
1.10.2. Hessegg
1.10.3. Investax
1.10.4. Nutanix
1.10.5. Protegrity
1.10.6. Visa
1.11. Whole Disk
1.11.1. CheckPoint Software
1.11.2. EgoSecure
1.11.3. Encryption Management
1.11.3.1. Wave Systems
1.11.4. McAfee
1.11.5. Microsoft
1.11.5.1. Bitlocker
1.11.6. Sophos
1.11.6.1. SafeGuard Enterprise (Utimaco)
1.11.7. Symantec (PGP)
1.11.8. Trustwave
1.11.8.1. DataControl
1.11.9. Vormetric
1.11.10. WinMagic
1.11.10.1. SecureDoc
2. Enterprise File Syncronization and Share
2.1. Blackberry
2.2. Box
2.3. Citrix
2.4. Covata
2.5. Dropbox
2.6. Egnyte
2.7. Google
2.8. Huddle
2.9. Intralinks
2.10. Kiteworks
2.11. Microsoft OneDrive
2.12. Syncplicity
2.13. Thru
2.14. Varonis
3. eSignatures
3.1. Adobe eSign Services
3.2. Alphatrust
3.3. Docusign
3.4. Hellosign
3.5. Rightsignature
3.6. Sertifi
4. File Analysis Software
4.1. Acaveo
4.2. Active Navigation
4.3. AvePoint
4.4. Beyond Recognition
4.5. Bloomberg
4.6. CommVault
4.7. Condrey
4.8. Covertix
4.9. DataGlobal
4.10. DataGravity
4.11. Equivio
4.12. HiSoftware
4.13. HP
4.13.1. Control Point
4.14. IBM
4.14.1. StoreIQ
4.15. Identifty Finder
4.16. Imperva
4.17. Index Engines
4.18. Kazoup
4.19. MailGuard
4.20. Novell
4.21. NTP Software
4.22. Nuix
4.23. Proofpoint
4.24. Stealthbits
4.25. ThinAir
4.26. Varonis
4.27. WatchDox
4.28. Whitebox Security
4.29. ZyLab
5. Hardware Security Modules (HSM)
5.1. Cloud HSM
5.1.1. Amazon
5.1.2. Azure
5.1.3. Google
5.1.4. IBM
5.2. Hardware
5.2.1. Entrust
5.2.2. FutureX
5.2.3. Futurex
5.2.4. HPE
5.2.5. Keyfactor
5.2.6. PrimeKey
5.2.7. Thales
6. Content Disarming and Reconstruction (CDR)
6.1. Check Point
6.2. DeepInstinct
6.3. Forcepoint
6.4. Fortinet
6.5. Garrison Technology
6.6. Glasswall
6.7. IronScales
6.8. ODI-X
6.9. OPSWAT
6.9.1. https://www.opswat.com/products/metascan/
6.10. Sasa Software
6.11. Symantec
6.12. Votiro
7. Data Classification and Tracking
7.1. Banyan Solutions
7.2. BoldonJames
7.3. Digital Guardian
7.4. HP
7.5. IBM
7.6. Identity Finder
7.7. Mach1 Development
7.8. Microsoft (Formerly Secure Islands)
7.9. MinerEye
7.10. Nuix
7.11. Smartlogic
7.12. Titus
7.13. Varonis
7.14. CoSoSys
8. Data Governance and Classification
8.1. Boldonjames
8.2. Expert Source
8.2.1. http://www.expertsource.in/index.php
8.3. HP
8.4. IBM
8.5. Informatica
8.6. Nuix
8.7. Somansa
8.8. Titus
8.9. ThinAir
9. Data Loss Prevention (DLP)
9.1. Endpoint
9.1.1. Mobile
9.1.1.1. Symantec
9.1.1.2. Websense
9.1.1.3. Microsoft (Secure Islands)
9.1.2. Windows
9.1.2.1. Absolute Software
9.1.2.2. CA Technologies
9.1.2.3. Digital Guardian
9.1.2.4. GTB Technologies
9.1.2.5. Infowatch
9.1.2.6. McAfee
9.1.2.7. RSA
9.1.2.8. Microsoft (Secure Islands)
9.1.2.9. Somansa
9.1.2.10. Symantec
9.1.2.11. Trustwave
9.1.2.12. Watchful Software
9.1.2.13. Raytheon-Websense
9.1.2.14. Zecurion
9.2. Network
9.2.1. Digital Guardian
9.2.2. Fidelis Security Systems (Subsidiary of General Dynamics)
9.2.3. Symantec
9.2.4. InfoWatch
9.3. Secure Email Gateway
9.3.1. Cisco
9.3.2. Symantec
9.3.3. McAfee
9.3.4. Somansa
9.4. Secure Web Gateway
9.4.1. McAfee
9.4.2. Symantec
9.4.3. Somansa
9.5. Breached Data Detection
9.5.1. Consumer
9.5.1.1. haveibeenpwned.com
9.5.1.1.1. https://haveibeenpwned.com/
9.5.2. Enterprise
9.5.2.1. Hold Security
9.5.2.1.1. http://holdsecurity.com/
9.5.2.2. Infoarmor
9.5.2.2.1. https://www.infoarmor.com/
9.5.2.3. Ionic
9.5.2.3.1. https://www.ionic.com/
9.5.2.4. SpyCloud
9.5.2.4.1. https://spycloud.com/
10. Database Security
10.1. Database Audit and Protection (DAP)
10.1.1. Application Security, Inc
10.1.2. BeyondTrust
10.1.3. Big Data Platform DAP
10.1.3.1. BlueTalon
10.1.3.2. Cloudera
10.1.3.2.1. Sentry
10.1.3.3. Hortonworks
10.1.3.3.1. Ranger
10.1.3.4. IBM
10.1.3.5. Imperva
10.1.4. DataSunrise
10.1.5. Datiphy
10.1.6. Fortinet
10.1.7. Hexatier
10.1.8. IBM
10.1.9. Imperva
10.1.10. IRI
10.1.10.1. Oracle
10.1.10.2. SQL Server
10.1.11. McAfee
10.1.12. Mentis Software
10.1.13. Oracle Corp
10.1.14. PentaSecurity
10.1.15. Warevalley
10.2. Database Activity Monitoring
10.2.1. Cyral
10.2.2. Datiphy
10.2.3. IBM
10.2.4. Imperva
10.2.5. Satori
10.2.6. Somansa
10.2.7. Trellix
10.3. Data Lake Security
10.3.1. Satori
10.3.2. SISense
