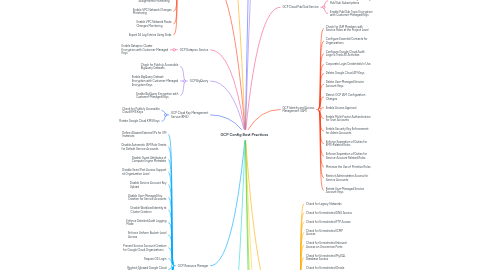
GCP Config Best Practices
von SecurityBoat Support
1. GCP Google Kubernetes Engine Service
1.1. Detect GCP Cloud DNS Configuration Changes
1.2. Detect GCP Cloud Storage Configuration Changes
1.3. Detect GCP GKE Configuration Changes
1.4. Enable Auto-Repair for GKE Cluster Nodes
1.5. Enable Auto-Upgrade for GKE Cluster Nodes
1.6. Enable Encryption for Application-Layer Secrets for GKE Clusters
1.7. Enable GKE Cluster Node Encryption with Customer-Managed Keys
1.8. Enable Integrity Monitoring for Cluster Nodes
1.9. Enable Secure Boot for Cluster Nodes
1.10. Restrict Network Access to GKE Clusters
1.11. Use Shielded GKE Cluster Nodes
2. GCP Cloud Logging
2.1. Enable Logs Router Encryption with Customer-Managed Keys
2.2. Enable Monitoring for Audit Configuration Changes
2.3. Enable Monitoring for Bucket Permission Changes
2.4. Enable Monitoring for Custom Role Changes
2.5. Enable Monitoring for Firewall Rule Changes
2.6. Enable Monitoring for SQL Instance Configuration Changes
2.7. Enable Project Ownership Assignments Monitoring
2.8. Enable VPC Network Changes Monitoring
2.9. Enable VPC Network Route Changes Monitoring
2.10. Export All Log Entries Using Sinks
3. GCP Dataproc Service
3.1. Enable Dataproc Cluster Encryption with Customer-Managed Keys
4. GCP BigQuery
4.1. Check for Publicly Accessible BigQuery Datasets
4.2. Enable BigQuery Dataset Encryption with Customer-Managed Encryption Keys
4.3. Enable BigQuery Encryption with Customer-Managed Keys
5. GCP Cloud Key Management Service(KMS)
5.1. Check for Publicly Accessible Cloud KMS Keys
5.2. Rotate Google Cloud KMS Keys
6. GCP Resource Manager
6.1. Define Allowed External IPs for VM Instances
6.2. Disable Automatic IAM Role Grants for Default Service Accounts
6.3. Disable Guest Attributes of Compute Engine Metadata
6.4. Disable Serial Port Access Support at Organization Level
6.5. Disable Service Account Key Upload
6.6. Disable User-Managed Key Creation for Service Accounts
6.7. Disable Workload Identity at Cluster Creation
6.8. Enforce Detailed Audit Logging Mode
6.9. Enforce Uniform Bucket-Level Access
6.10. Prevent Service Account Creation for Google Cloud Organizations
6.11. Require OS Login
6.12. Restrict Allowed Google Cloud APIs and Services
6.13. Restrict Authorized Networks on Cloud SQL instances
6.14. Restrict Default Google-Managed Encryption for Cloud SQL Instances [Deprecated]
6.15. Restrict Load Balancer Creation Based on Load Balancer Types
6.16. Restrict Public IP Access for Cloud SQL Instances at Organization Level
6.17. Restrict Shared VPC Subnetworks
6.18. Restrict VPC Peering Usage
6.19. Restrict VPN Peer IPs
6.20. Restrict Virtual Machine IP Forwarding
6.21. Restrict the Creation of Cloud Resources to Specific Locations
6.22. Restricting the Use of Images
6.23. Skip Default VPC Network Creation
7. GCP Cloud Storage
7.1. Check for Publicly Accessible Cloud Storage Buckets
7.2. Check for Sufficient Data Retention Period
7.3. Configure Retention Policies with Bucket Lock
7.4. Enable Lifecycle Management for Cloud Storage Objects
7.5. Enable Object Encryption with Customer-Managed Keys
7.6. Enable Object Versioning for Cloud Storage Buckets
7.7. Enable Uniform Bucket-Level Access for Cloud Storage Buckets
8. GCP API
8.1. Check for API Key API Restrictions
8.2. Check for API Key Application Restrictions
8.3. Enable Cloud Asset Inventory
8.4. Rotate Google Cloud API Keys
9. GCP Cloud SQL
9.1. Check for Cloud SQL Database Instances with Public IPs
9.2. Check for MySQL Major Version
9.3. Check for PostgreSQL Major Version
9.4. Check for Publicly Accessible Cloud SQL Database Instances
9.5. Configure"log_min_error_statement" Flag for PostgreSQL Database Instances
9.6. Configure "max_connections" Flag for PostgreSQL Database Instances
9.7. Configure 'user connections' Flag for SQL Server Database Instances
9.8. Configure Automatic Storage Increase Limit
9.9. Configure Root Password for MySQL Database Access
9.10. Disable "Contained Database Authentication" Flag for SQL Server Database Instances
9.11. Disable "Cross DB Ownership Chaining" Flag for SQL Server Database Instances
9.12. Disable "local_infile" Flag for MySQL Database Instances
9.13. Disable "log_min_duration_statement" Flag for PostgreSQL Database Instances
9.14. Disable "log_planner_stats" Flag for PostgreSQL Database Instances
9.15. Disable '3625' Trace Flag for SQL Server Database Instances
9.16. Disable 'external scripts enabled' Flag for SQL Server Database Instances
9.17. Disable 'log_executor_stats' Flag for PostgreSQL Database Instances
9.18. Disable 'log_parser_stats' Flag for PostgreSQL Database Instances
9.19. Disable 'log_statement_stats' Flag for PostgreSQL Database Instances
9.20. Disable 'remote access' Flag for SQL Server Database Instances
9.21. Disable 'user options' Flag for SQL Server Instances
9.22. Enable "log_checkpoints" Flag for PostgreSQL Database Instances
9.23. Enable "log_checkpoints" Flag for PostgreSQL Database Server Configuration
9.24. Enable "log_connections" Flag for PostgreSQL Database Instances
9.25. Enable "log_disconnections" Flag for PostgreSQL Database Instances
9.26. Enable "log_lock_waits" Flag for PostgreSQL Database Instances
9.27. Enable "log_temp_files" Flag for PostgreSQL Database Instances
9.28. Enable "skip_show_database" Flag for MySQL Database Instances
9.29. Enable "slow_query_log" Flag for MySQL Database Servers
9.30. Enable 'cloudsql.enable_pgaudit' and 'pgaudit.log' Flags for PostgreSQL Database Instances
9.31. Enable 'log_hostname' Flag for PostgreSQL Database Instances
9.32. Enable Automated Backups for Cloud SQL Database Instances
9.33. Enable Automatic Storage Increase
9.34. Enable Cloud SQL Instance Encryption with Customer-Managed Keys
9.35. Enable High Availability for Cloud SQL Database Instances
9.36. Enable Point-in-Time Recovery for MySQL Database Instances
9.37. Enable SSL/TLS for Cloud SQL Incoming Connections
9.38. Rotate Server Certificates for Cloud SQL Database Instances
10. GCP Cloud Pub/Sub Service
10.1. Enable Dead Lettering for Google Pub/Sub Subscriptions
10.2. Enable Pub/Sub Topic Encryption with Customer-Managed Keys
11. GCP Identity and Access Management (IAM)
11.1. Check for IAM Members with Service Roles at the Project Level
11.2. Configure Essential Contacts for Organizations
11.3. Configure Google Cloud Audit Logs to Track All Activities
11.4. Corporate Login Credentials In Use
11.5. Delete Google Cloud API Keys
11.6. Delete User-Managed Service Account Keys
11.7. Detect GCP IAM Configuration Changes
11.8. Enable Access Approval
11.9. Enable Multi-Factor Authentication for User Accounts
11.10. Enable Security Key Enforcement for Admin Accounts
11.11. Enforce Separation of Duties for KMS-Related Roles
11.12. Enforce Separation of Duties for Service-Account Related Roles
11.13. Minimize the Use of Primitive Roles
11.14. Restrict Administrator Access for Service Accounts
11.15. Rotate User-Managed Service Account Keys
12. GCP VPC
12.1. Check for Legacy Networks
12.2. Check for Unrestricted DNS Access
12.3. Check for Unrestricted FTP Access
12.4. Check for Unrestricted ICMP Access
12.5. Check for Unrestricted Inbound Access on Uncommon Ports
12.6. Check for Unrestricted MySQL Database Access
12.7. Check for Unrestricted Oracle Database Access
12.8. Check for Unrestricted Outbound Access on All Ports
12.9. Check for Unrestricted PostgreSQL Database Access
12.10. Check for Unrestricted RDP Access
12.11. Check for Unrestricted RPC Access
12.12. Check for Unrestricted SMTP Access
12.13. Check for Unrestricted SQL Server Access
12.14. Check for Unrestricted SSH Access
12.15. Check for VPC Firewall Rules with Port Ranges
12.16. Default VPC Network In Use
12.17. Enable Cloud DNS Logging for VPC Networks
12.18. Enable Logging for VPC Firewall Rules
12.19. Enable VPC Flow Logs for VPC Subnets
12.20. Exclude Metadata from Firewall Logging
13. GCP Cloud Load Balancing
13.1. Check for Insecure SSL Cipher Suites
13.2. Detect GCP Load Balancer Configuration Changes
13.3. Enable HTTPS for Google Cloud Load Balancers
13.4. Enable Logging for HTTP(S) Load Balancing Backend Services
14. GCP Compute Engine
14.1. Approved Virtual Machine Image in Use
14.2. Check for Desired Machine Type(s)
14.3. Check for Instance-Associated Service Accounts with Full API Access
14.4. Check for Instances Associated with Default Service Accounts
14.5. Check for Publicly Shared Disk Images
14.6. Check for Virtual Machine Instances with Public IP Addresses
14.7. Configure Maintenance Behavior for VM Instances
14.8. Detect GCP Compute Engine Configuration Changes
14.9. Disable Auto-Delete for VM Instance Persistent Disks
14.10. Disable IP Forwarding for Virtual Machine Instances
14.11. Disable Interactive Serial Console Support
14.12. Disable Preemptibility for VM Instances
14.13. Enable "Block Project-Wide SSH Keys" Security Feature
14.14. Enable "Shielded VM" Security Feature
14.15. Enable Automatic Restart for VM Instances
14.16. Enable Confidential Computing for Virtual Machine Instances
14.17. Enable Deletion Protection for VM Instances
14.18. Enable Instance Group Autohealing
14.19. Enable OS Login for GCP Projects
14.20. Enable VM Disk Encryption with Customer-Supplied Encryption Keys
14.21. Enable Virtual Machine Disk Encryption with Customer-Managed Keys
14.22. Enforce HTTPS Connections for App Engine Applications
14.23. Remove Old Persistent Disk Snapshots
14.24. Use OS Login with 2FA Authentication for VM Instances
15. GCP Domain Name System (DNS)
15.1. Check for DNSSEC Key-Signing Algorithm in Use
15.2. Check for DNSSEC Zone-Signing Algorithm in Use
15.3. Enable DNSSEC for Google Cloud DNS Zones