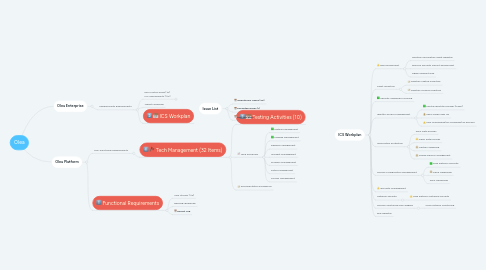
1. Olea Enterprise
1.1. Cybersecurity Requirements
1.1.1. Key Control Areas (10) ICS Assessments (110)
1.1.1.1. 1. Foo
1.1.1.2. 2. Bar
1.1.1.3. 3. Baz
1.1.2. Threat Modelling
1.1.3. ICS Workplan
2. Olea Platform
2.1. Non-Functional Requirements
2.1.1. Tech Management (32 Items)
2.1.1.1. Testing Activities (10)
2.1.1.2. Tech Processes
2.1.1.2.1. Testing Management
2.1.1.2.2. Change Management
2.1.1.2.3. Release Management
2.1.1.2.4. Incident Management
2.1.1.2.5. Problem Management
2.1.1.2.6. Patch Management
2.1.1.2.7. Access Management
2.1.1.3. Documentation & Evidence
2.2. Functional Requirements
2.2.1. User Stories (114)
2.2.2. Backlog+Roadmap
2.2.3. Defect Log
3. ICS Workplan
3.1. Risk Assessment
3.1.1. Maintain Information Asset Register
3.1.2. Perform Security Impact Assessment
3.1.3. Agree Inherent Risk
3.2. Asset Inventory
3.2.1. Maintain Laptop Inventory
3.2.2. Maintain License Inventory
3.3. Security Awareness Training
3.4. Identity Access Management
3.4.1. Central Identity Provider (O365)
3.4.2. SaaS Single Sign On
3.4.3. User onboarding/off-boarding/HR process
3.5. Information Protection
3.5.1. AWS Data Policies
3.5.2. O365 Data Policies
3.5.3. Laptop Hardening
3.5.4. Mobile Device Management
3.6. Secure Configuration Management
3.6.1. Olea Platform Security
3.6.2. O365 Hardening
3.6.3. AWS Hardening
3.7. 3rd Party Management
3.8. Network Security
3.8.1. Olea Platform Network Security
3.9. Secure Monitoring and Logging
3.9.1. Olea Platform Monitoring
