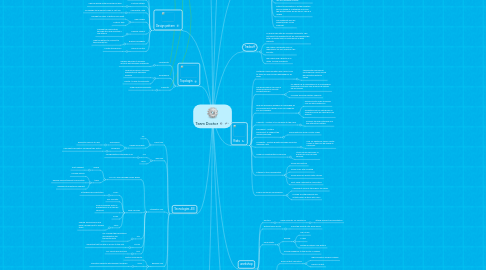
1. Stakeholders
1.1. Health care industry
1.1.1. Doctor/Consultants
1.1.2. Hospitals
1.1.2.1. NorthAmerica
1.1.2.2. Europe
1.1.2.3. Asia
1.1.3. Hospital Management Comittee
1.2. Architect
1.2.1. Lead the team responsible for the design
1.2.2. Implementation
1.2.3. ongoing management
2. System Qualities
2.1. Availability
2.2. Security
2.2.1. Web Services
2.2.1.1. WS-Security
2.2.1.1.1. XML Signature. To achieve message authentication and integrity
2.2.1.1.2. XML Encription. To achieve message confidentiality
2.2.1.1.3. Security Tokens- To achieve Authentication and autorization
2.2.1.2. EJB
2.2.1.2.1. JAAS
2.3. Extensibility
2.4. Scalability
2.4.1. Load Balancer
3. Tecnologies JEE
3.1. Client Tier
3.1.1. PC
3.1.2. Design Principles
3.1.2.1. Affordance
3.1.2.1.1. Elements obvious to user
3.1.2.2. Feedback
3.1.2.2.1. User sent information following their action
3.2. Web Tier
3.2.1. JSF
3.2.1.1. Para garantizar interfaces ricas
3.2.2. JAAS
3.3. Integration Tier
3.3.1. JMS API and Message Driven Beans
3.3.1.1. queue
3.3.1.1.1. Post Request
3.3.1.2. topic
3.3.1.2.1. Provide Advice
3.3.1.2.2. Review Advice/Request Clarification
3.3.1.2.3. Respond to Additional Request
3.3.2. Web Services
3.3.2.1. SAAJ
3.3.2.1.1. Attaching documentation
3.3.2.2. WS-Security
3.3.2.3. Para la conexión entre la presentacion y la capa de servicios
3.3.2.4. SOAP
3.3.2.5. UDDI
3.3.2.5.1. Publish web services and have a single point to access them
3.3.3. JPA
3.3.3.1. For manage the persistence and garantice the transactionality
3.3.4. HTTPS
3.3.4.1. Garantice that the site is secure to the user
3.3.5. RMI
3.3.5.1. For clients who are java
3.4. Bussines Tier
3.4.1. Gestor Documental
3.4.2. JAAS
3.4.2.1. Garantice security with different modules
3.4.3. EJB
3.4.3.1. It provides the bussines logic
3.5. EIS Tier
3.5.1. Relational Database
3.5.2. LDAP Server
4. Design pattern
4.1. Proxy Pattern
4.1.1. Manejo de imagenes
4.2. Bussines Delegate
4.3. Factory Pattern
4.3.1. Choose which system should be used
4.4. Composite View
4.4.1. To manage the different views in just one
4.5. View Helper
4.5.1. Manage the logic of data access apart
4.5.2. Custom tags
4.6. Transfer Object
4.6.1. Manage the information through dtos and maintain a low latency
4.7. Bussines Delegate
4.7.1. Hide the details to connect to the bussines tier
4.8. Service Locator
4.8.1. Locate the services
5. Topologia
5.1. Modularility
5.1.1. Medium because it increase security but decrease availability
5.2. Redudancy
5.2.1. Medium because it increase availavility but decrease security
5.2.2. Cluster to help to availavility
5.3. Capacity
5.3.1. High because availavility
6. Justification
6.1. Adoption of Information Tecnology
6.1.1. Make available remote online resources to the doctors/consultants
6.1.2. Improve access of consultants
6.1.3. Reducing costs of access to specialiced resources
6.1.3.1. Invest the savings in improving other parts of the hospital
6.2. Limitations
6.2.1. Schedule
6.2.2. Budget
6.3. Define Project Development Measurement
6.3.1. KPI's
7. Assumptions
7.1. The system will be accesed by pcs through internet
7.2. It is assumed that cliente tier has affordance, usability and feedback
7.3. It's assumed that the web services are used for all external clients. This is just for readonly and for external clients that need this service
7.4. 5. The performance it's important because it’s a manifest quality and we are going to give quick responses to the user. This can be achieved with the use of load balancing and jms. a. Load balancing allow us process requests asynchronic quickly as the insertion in local database and access to web presentation b. JMS allow put process in queue for giving a quick response and let the system process the request later.
7.5. 6. We are going to publish the web services with UDDI for external clientes. This ensure that there will be an only access point
7.6. There will be a LDAP server who has all the security, users, roles and priviledeges for all the system
7.7. The web services only will be used for clients who arent java, otherwise we will use RMI because is faster
7.8. patient's information in all the hospitals will be loaded in a database local and the identification will be the id. This id is unique
7.9. The scalability well be garanticed by a load balancer.
8. Project Information
8.1. Component Diagram
8.2. Class Diagram
8.3. Deployment Diagram
8.4. Interaction Diagrams
8.5. Risk and Mitigarion Risks
9. workshop
9.1. Doctors
9.1.1. Place requests for assistance
9.1.1.1. attach relevant documentation
9.2. system team doctor
9.2.1. Place the request into work queue
9.3. Consultants
9.3.1. Review
9.3.1.1. MRI Scans
9.3.1.2. X-rays
9.3.1.3. Review a patiens case history
9.3.2. Provide feedback to the doctor in charge
9.4. Systems
9.4.1. Rich content repository
9.4.1.1. high resolution medical images
9.4.1.2. binary content
9.4.2. Patient Record System
9.4.2.1. Medical History
9.4.3. Prescription database
9.4.4. Acceso
9.4.4.1. Web Services to read data
9.4.4.2. When doctors/consultans access the system remotely it will be in read-only
9.4.5. The system will save any action over any of the systems
9.5. Patients are identified by a unique ID
10. Risks
10.1. Network Communication and Layout. Due to there are many zones geographicly far away
10.1.1. Implementar alarmas de contingencia a nivel de red qeu permitan detectar caidas
10.2. The performance can have a delay because of security and distribucion
10.2.1. No abusar de la redundancia y la modularidad realizando controles con pruebas de estress de las mismas
10.2.2. Increase de server system capacity
10.3. Que los servidores excedan su capacidad de almacenamiento debido a que las imagenes son muy grandes
10.3.1. Generar políticas de archiving con los datos historicos
10.3.2. Garantizar que los servidores no superen el 80% de capacidad con alarmas
10.4. Usability - System is too complex to the users
10.4.1. Simplify the user interface and the interaction pattern
10.5. Througput - System insufficient to support the desired workload
10.5.1. Add Additional server cluster nodes
10.6. Scalability - System growth exceeds expected maximum rate
10.6.1. Plan for additional server cluster nodes so they can be added as necessary
10.7. Need for redistributing of services
10.7.1. Utilice some mecanism of publish as UDDI for web services
10.8. Attacks to the vulnerabilities
10.8.1. Avoid sql injection
10.8.2. Avoid cross-site scripting
10.8.3. Avoid denial of service with catchas
10.8.4. Dont show confidential information
10.9. Fuga Informacion confidencial
10.9.1. Implement security through all the layers
10.9.2. Provide an authorizacion and autentication system with JASS

