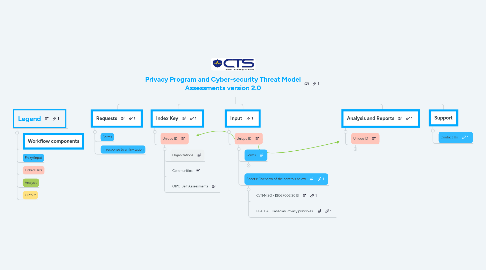
1. Legend
1.1. Workflow components
1.2. Entry/Input
1.3. Linked Data
1.4. Analysis
1.5. Output
2. Requests
2.1. Forms
2.2. In response to an Invitation
3. Index Key
3.1. Unique ID
3.1.1. Organizations
3.1.2. Communities
3.1.3. OIPC-Self Assessments
4. Input
4.1. Unique ID
4.1.1. Forms
4.1.1.1. OIPC Self-Assessments: CTS Website
4.1.1.1.1. Part I: CTS Website
4.1.1.1.2. Part II: CTS Website
4.1.1.1.3. Part III: CTS Website
4.1.1.1.4. Part IV: CTS Website
4.1.1.2. CsTM - Cyber-security Threat Model Assessments
4.1.1.2.1. CsTM-CCCS
4.1.1.3. PPA - Privacy Program Assessments
4.1.1.3.1. PPA-BC - British Columbia PIPA: CTS Website
4.1.1.4. Recommendations
4.1.1.4.1. Organizations
4.1.1.4.2. Community-wide
4.1.2. Sheets: Overview of the controls below
4.1.2.1. CsTM-ISO - ISO27002:2013
4.1.2.2. PPA-CA - Canadian Privacy principles.
5. Analysis and Reports
5.1. Unique ID
5.1.1. Import
5.1.1.1. Selected Organization Forms
5.1.1.2. Selected Community Forms
5.1.2. Analysis
5.1.2.1. Organization
5.1.2.2. Community-wide
5.1.2.3. Methodology
5.1.2.3.1. An assessor rates the client's response to a given control based on maturity ratings established in Configuration settings. Rating definitions, established according to published control standards will appear on the data entry page.
5.1.2.3.2. Each question is pre-configured to determine the relative impact (importance) by selecting the broad areas that it might affect.
5.1.2.3.3. The weight of each control question is then calculated relative to others.
5.1.2.3.4. The combined values of the Scores compared with what they would have been had they been "Perfect" are used in the Analysis Tab to produce overall sum of the Privacy Program Assessment (PPA-BC) and Cybersecurity Threat Modelling (CsTM)
5.1.2.3.5. Overall Score is based on an assessment of the relative value of PPA-BC or PPA-CA compared with CsTM. By default, they are weighted equally, but it can be adjusted in Configuration settings depending on the internal priorities and nature of the community being assessed.
5.1.2.3.6. These values are summarized graphical reports together with:
5.1.3. Reports
5.1.3.1. Organizations
5.1.3.1.1. Graphical Summary with Executive Recommendations
5.1.3.2. Community-wide
5.1.3.2.1. Graphical Summary with Executive Recommendations
