INTRUSION DETECTION SYSTEM
Door istm gwu
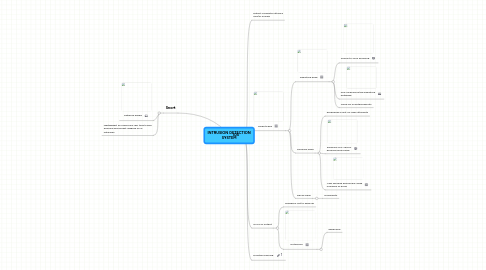
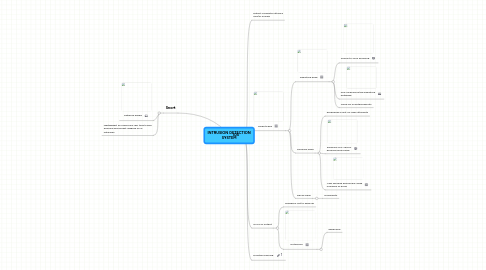
1. Snort
1.1. Network based
1.2. lightweight IDS performs real time traffic analysis and packet logging on IP networks
2. IDS
2.1. Detect computer attacks and/or misuse
2.2. Three types
2.2.1. Signature base
2.2.1.1. Similar to virus scanning
2.2.1.2. only as good as the signature database
2.2.1.3. Good for scripted exploits
2.2.2. Anomaly base
2.2.2.1. exceeding a limit on login attempts
2.2.2.2. Finding a NIC card in promiscuous mode
2.2.2.3. User sending abnormally large numbers of email
2.2.3. Decoy base
2.2.3.1. Honeypots
2.3. ALOT of output
2.3.1. Tendency not to keep up
2.3.2. Outsource
2.3.2.1. expensive
