Chapter 11 Computer Security
af Bodeethorn Sirakantarat
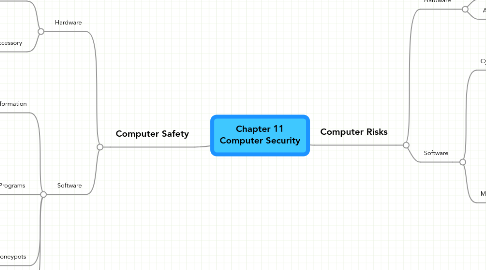
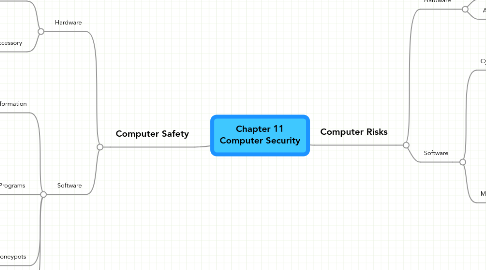
1. Computer Safety
1.1. Hardware
1.1.1. Protect Theft
1.1.1.1. Real time location system
1.1.1.2. Lock
1.1.2. Accessory
1.1.2.1. Soft Case
1.1.2.2. Air Cooling
1.1.2.3. UPS
1.2. Software
1.2.1. Protect Information
1.2.1.1. Encryption
1.2.1.2. Change Password
1.2.1.3. Lock file
1.2.2. Antivirus Programs
1.2.2.1. McAfee
1.2.2.2. Norton
1.2.2.3. Avira
1.2.2.4. AVG
1.2.2.5. Kaspersky
1.2.3. Honeypots
1.2.3.1. Research Honeypot
1.2.3.2. Production Honeypot
1.2.4. Back up
2. Computer Risks
2.1. Hardware
2.1.1. Theft
2.1.2. Accident
2.2. Software
2.2.1. Cybercrime
2.2.1.1. Hacker
2.2.1.2. Cracker
2.2.1.3. Script Kiddie
2.2.1.4. Cyberterrorist
2.2.2. Malware
2.2.2.1. Virus
2.2.2.2. Worm
2.2.2.3. Troian
2.2.2.4. Spyware
2.2.2.5. Phishing
2.2.2.6. Zombie Network
2.2.2.7. Keylogger
2.2.2.8. Dialer
2.2.2.9. Hybrid Malware
