Hearst Mobile Device Secuirty
af andrew leach
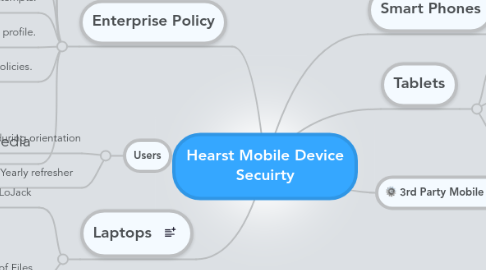
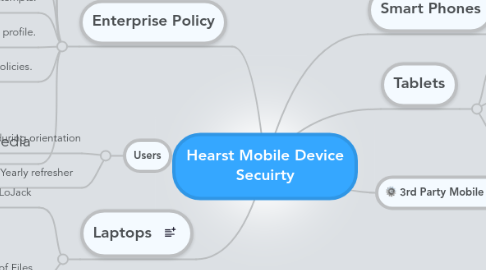
1. Laptops
1.1. LoJack
1.1.1. Provides audit trail if data is stolen
1.1.2. Locate Stolen/Lost machine
1.2. Encryption of Files
1.2.1. Folder Based File Encryption for sentive documents
1.2.2. Hard disk encryption
2. Enterprise Policy
2.1. Require email session encryption.
2.2. Wipe devices if they are lost or stolen.
2.3. Protect devices with a passcode lock.
2.4. Autolock devices after periods of inactivity.
2.5. Autowipe devices after failed unlock attempts.
2.6. Protect the configuration profile.
2.7. Continuously refresh policies.
2.8. Portable Media
2.8.1. Flash Drives
2.8.1.1. Encrypting flash drives
2.8.1.2. Policys Can be set to only Allow Approved Drives
2.8.2. CD/DVD
3. Users
3.1. Training on Mobile Device during orientation
3.2. Yearly refresher
4. Smart Phones
4.1. Andriod
4.2. iPhone
4.2.1. Exchange Provides Mobile Wipe
5. Tablets
5.1. iPad
5.2. Kindle
5.2.1. Kindle presents unique security challenge
