Chapter XI Computer Security And Privacy
by P Otenta
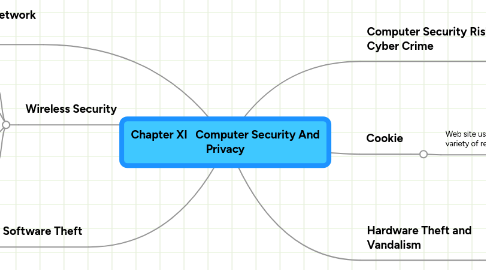
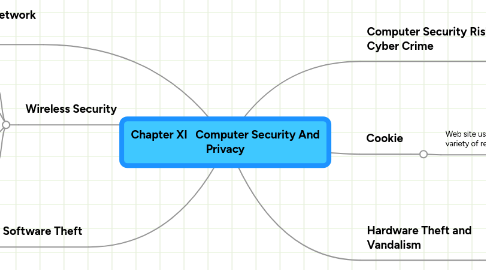
1. Internet and Network Attacks
1.1. Computer Virus
1.2. Trojan Horse
1.3. Worm
1.4. Rootkit
2. Software Theft
2.1. Steals software media
2.2. Intentionally erases programs
2.3. illegally copies a program
2.4. illegally registers or actives a program
3. Wireless Security
3.1. A wireless access point should not broadcast an SSID
3.2. Change the default SSID
3.3. Configure a WAP so that only certain devices can access it
3.4. Use WPA or WPA2 security standards
4. Computer Security Risk & Cyber Crime
4.1. Crackers
4.1.1. New node
4.2. Hackers
4.3. Script Kiddies
4.4. Corporate Spies
4.5. Unethical Employees
4.6. Cyberextortionists
4.7. Cyberterrorists
5. Hardware Theft and Vandalism
5.1. Physical access controls
5.2. Alarm systems
5.3. Cables to lock equipment
5.4. Real time location system
5.5. Password,possessed objects,and biometrics
6. Cookie
6.1. Web site use cookies for a variety of reasons
6.1.1. Allow for personalization
6.1.2. Store users passwords
6.1.3. Assist with online shopping
6.1.4. Track how often users visit a site
6.1.5. Target advertisements
