1. Google
1.1. Android Security Best Practices
1.1.1. Enforce secure communication Safeguard communication between apps
1.1.2. Show an app chooser
1.1.3. Disallow access to your app's content providers
1.1.4. Use TLS traffic
1.1.5. Add a network security configuration
1.1.6. Create your own trust manager
1.1.7. Use HTML message channels
1.2. App Security Best Practices
1.2.1. Data storage-1
1.2.2. Internal storage-1
1.2.3. Internal storage-2
1.2.4. External storage-1
1.2.5. External storage-2
1.2.6. Content providers-1
1.2.7. Content providers-2
1.2.8. Content providers-3
1.2.9. Content providers-4
1.2.10. Content providers-5
1.2.11. Content providers-6
1.2.12. Permissions-1
1.2.13. Permission requests-1
1.2.14. Permission requests-2
1.2.15. Permission requests-3
1.2.16. Permission requests-4
1.2.17. Permission definitions-1
1.2.18. Permission definitions-2
1.2.19. Permission definitions-3
1.2.20. Permission definitions-4
1.2.21. Networking-1
1.2.22. IP networking-1
1.2.23. IP networking-2
1.2.24. IP networking-3
1.2.25. IP networking-4
1.2.26. Telephony networking-1
1.2.27. Telephony networking-2
1.2.28. Stay vigilant-2
1.2.29. Usage and access control-4
1.2.30. Usage and access control-6
1.2.31. Key rotation and expiration-1
1.2.32. General best practices-1
1.2.33. General best practices-2
1.2.34. General best practices-4
1.2.35. General best practices-5
1.2.36. Cryptography-3
1.2.37. Interprocess communication-1
1.2.38. Intents-1
1.2.39. Intents-2
1.2.40. Intents-4
1.2.41. Binder and Messenger interfaces-1
1.2.42. Binder and Messenger interfaces-2
1.2.43. Broadcast receivers-2
1.2.44. Security in a virtual machine-3
1.3. Core App Quality
1.3.1. PS-T5
1.3.2. SC-N2
1.3.3. SC-N3
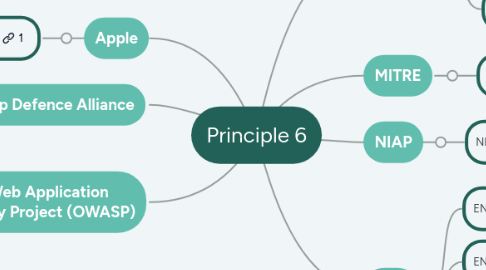
2. Apple
2.1. Apple Developer Security
2.1.1. Secure Data Preventing Insecure Network Connections Overview
2.1.2. Secure Data Preventing Insecure Network Connections Prefer High-Level Frameworks in Your App
2.1.3. Launch environmental constraints Applying launch environment and library constraints Overview
2.1.4. Legacy Interfaces Secure Transport Overview
2.1.5. Legacy Interfaces Secure Download Overview
3. MITRE
3.1. ATT&CK Mobile Application Developer Guidance
3.1.1. Secure API Design
3.1.2. Threat Modeling in the Design Phase
4. App Defence Alliance
4.1. Application Security Assessment
4.1.1. Mobile 1.4.1.1 (Android)
4.1.2. Mobile 1.4.1.2 (Android)
4.1.3. Mobile 1.4.1.3 (Android)
4.1.4. Web 4.1.1
4.1.5. Web 4.1.2
4.1.6. Web 4.1.4
4.1.7. Web 5.1.1
4.1.8. Web 5.1.2
4.1.9. Web 5.1.3
4.1.10. Web 5.1.4
4.1.11. Web 5.1.5
4.1.12. Web 5.1.6
4.1.13. Web 5.1.7
4.1.14. Web 5.1.8
4.1.15. Web 5.1.9
4.1.16. Web 5.1.10
4.1.17. Web 5.2.1
4.1.18. Cloud 1.3.1
4.1.19. Cloud 4.1.1
4.1.20. Cloud 4.2.2
4.1.21. Cloud 5.3.1
4.1.22. Cloud 5.3.2
4.1.23. Cloud 6.3.1
4.1.24. Cloud 6.3.2
4.1.25. Cloud 6.3.3
4.1.26. Cloud 6.3.4
5. NIAP
5.1. NIAP Profile Protection
5.1.1. 5.1.6 Trusted Path/Channel (FTP) FTP_DIT_EXT.1 Protection of Data in Transit FTP_DIT_EXT.1.1
5.1.2. FCS_HTTPS_EXT.1.1
5.1.3. FCS_HTTPS_EXT.1.2
5.1.4. FCS_HTTPS_EXT.2.1
6. Open Web Application Security Project (OWASP)
6.1. Application Security Verification Standard 5.0.0 (ASVS)
6.1.1. V3.4 Browser Security Mechanism Headers
6.1.2. V3.5 Browser Origin Separation
6.1.3. V3.7 Other Browser Security Considerations
6.1.4. V4.1 Generic Web Service Security
6.1.5. V4.2 HTTP Message Structure Validation
6.1.6. V4.4 WebSocket
6.1.7. V12.1 General TLS Security Guidance
6.1.8. V12.2 HTTPS Communication with External Facing Services
6.1.9. V12.3 General Service to Service Communication Security
6.1.10. V13.1 Configuration Documentation
6.1.11. V13.2 Backend Communication Configuration
6.1.12. V16.4 Log Protection
6.1.13. V17.2 Media
6.2. Mobile Application Security Verification Standard (MASVS)
6.2.1. MASVS-NETWORK-1
6.2.2. MASVS-PLATFORM-1
7. ETSI
7.1. EN 303 645
7.1.1. Principle 5.4-3
7.1.2. Principle 5.5-6
7.1.3. Principle 5.5-7
7.1.4. Principle 5.6-2
7.1.5. Principle 5.6-3
7.1.6. Principle 5.6-4A
7.1.7. Principle 5.6-4B
7.1.8. Principle 5.6-9
7.1.9. Principle 5.9-1
7.1.10. Principle 5.12-1
7.2. EN 319 401
7.2.1. REQ-7.8-01
7.3. TS 103 606
7.3.1. 11.2.1 Mutual TLS Authentication 11.2.1.1 Overview
7.3.2. 11.2.1 Mutual TLS Authentication 11.2.1.2.1 Client certificate overview
7.3.3. 11.2.1 Mutual TLS Authentication 11.2.1.2 Client certificate 11.2.1.2.2 Operational considerations
7.3.4. 11.2.1 Mutual TLS Authentication 11.2.1.2 Client certificate 11.2.1.2.3 Client Root and Intermediate Certificate Authority Certificate Profiles
7.3.5. 11.4 CI Plus 11.4.1 CI Plus communication
7.4. TS 103 732
7.4.1. FAP_RSK.4
7.4.2. FAP_RSK.5
7.4.3. APA_LST.1-1
