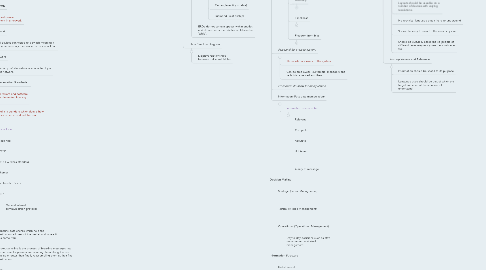
1. Misc
1.1. Efficiency
1.1.1. Expression of how little time, cost and effort is involved.
1.2. Effectiveness
1.2.1. Defined by quality of output, accuracy, presentation and comprehensiveness.
1.3. 8 MARK QUESTIONS
1.3.1. List functions used (they may be simple).
1.3.2. List test data to test the supplied option of solution.
1.4. Avoiding ethical problems
1.4.1. Publish a code of ethics which staff must formally sign up to before they are allowed to resume work.
1.4.2. Set up a decision support framework to guide management.
1.4.3. Establish appropriate consequences for violations of the code.
1.5. Mock Up Features
1.5.1. Big, bold headings; smaller body text
1.5.2. Logo
1.5.3. Site relevent images
1.5.4. Nav Bar with underlined links
1.5.5. Privacy Policy in footer
2. TOPIC 1: Problem Solving Methodology
2.1. Analysis
2.1.1. Define the problem addressing the following
2.1.1.1. Scope
2.1.1.1.1. Overview of the solution to which the client can understand what the solution will be capable of as well as how they will benefit from it.
2.1.1.2. Requirements
2.1.1.3. Constraints
2.1.1.3.1. Techical
2.1.1.3.2. Non Technical
2.2. Design
2.2.1. Plan the created solution through design tools and create the evaluation criteria.
2.3. Development
2.3.1. Create your solution with hardware and software.
2.3.2. Test and validate procedures whilst they are being created
2.3.2.1. Testing should occur whilst the product is developed and should generally follow a test plan.
2.3.2.1.1. Test plans address
2.3.2.1.2. User acceptance testing is a measurement of how well a user is suited to the solution.
2.3.2.2. Validation is a check of accuracy, completeness and reasonableness and is either done manually through the use of human proofreading OR electronically through use of rules.
2.3.2.2.1. Electronic Validation Rules Include
2.3.3. Create the user documentation.
2.3.3.1. On screen user documentation is created to guide users when using a solution. User documentation types are
2.3.3.1.1. Instruction Manuals
2.3.3.1.2. Quick start guides
2.3.3.1.3. Read me files
2.3.3.1.4. Tutorials
2.3.3.1.5. Help files
2.3.3.1.6. Tool tips
2.3.3.1.7. FAQ
2.4. Evaluation
2.4.1. Determine if the solution meets the needs of its users.
2.4.1.1. Time needs to be allocated for the users to actually use the solution before asking them to evaluate it.
2.4.1.2. Evaluation methods include surveys and interviews.
3. TOPIC 2: Data Networks
3.1. Network Categories
3.1.1. LAN
3.1.1.1. Small area each computer/device is a NODE.
3.1.2. WAN
3.1.2.1. Large area or when communications are carried by someone who is not a part of the organisation.
3.1.2.2. MAN (covers a city)
3.1.2.3. State Wide (covers a state)
3.1.2.4. NAN (covers a national area)
3.1.2.5. World Wide (Internet)
3.2. Network Architecture
3.2.1. Client/Server
3.2.1.1. Directional server with only one host that sends files to individual users.
3.2.1.2. Multitasks to handle multiple processes.
3.2.2. Other servers include
3.2.2.1. File
3.2.2.2. Print
3.2.2.3. Database
3.2.2.4. Web
3.2.2.5. DNS
3.2.2.6. Proxy
3.2.2.6.1. Proxy servers sit between the client and the internet. When a client requests a website their ip gets substituted for the proxy ip. The client is then anonymous and the accessed page becomes cache for possible later use.
3.2.2.7. Backup
3.2.3. P2P (peer to peer)
3.2.3.1. Direct file sharing between computers, users can connect, copy and edit files on another connected users computer.
3.2.4. Intranet
3.2.4.1. Secured closed LAN for organisations to share information whilst not sharing with public.
3.3. Network Topology
3.3.1. The physical device arrangement in a network.
3.3.2. Star Network
3.3.2.1. All devices connected to a switch meaning if a cable fails only the device on its line will fail.
3.3.3. Tree Network
3.3.3.1. Made up of star networks connected by a bus network.
3.4. Network Communication Standards
3.4.1. Ensure hardware and software can be implemented into any network.
3.4.2. A protocol is a standard which details how two devices on a network will transmit data.
3.4.3. Standards include
3.4.3.1. Token ring
3.4.3.2. TCP/IP
3.4.3.3. 802.11 wireless standard
3.4.3.4. Ethernet
3.4.3.5. File Transfer Protocol
3.4.3.6. HTTP
3.4.3.6.1. General internet communication protocol
3.4.4. Packets
3.4.4.1. Contains data chunks which hold the destination address of the packet and where it has come from.
3.4.4.2. Packet switching is the process of breaking messages into several smaller packets and sending them along the best available routes then finally reassembling them at their final destination.
3.5. Network Utilities
3.5.1. Network Operating System (NOS)
3.5.1.1. Controls server traffic, defining device communication
3.5.1.2. Controls file access, print queues, authentication etc.
3.5.2. Network Software
3.5.2.1. Email
3.5.2.2. File Transfer Protocol
3.5.2.3. IM
3.5.2.4. Web Browsers
3.5.2.5. Webpage Editor (dreamweaver)
3.5.2.6. TCP/IP protocols for communication
3.5.3. Network Hardware
3.5.3.1. Wireless Access Point
3.5.3.1.1. Wireless connection of a user to a wired or wireless network.
3.5.3.2. Roaming
3.5.3.2.1. Wireless connection to a network with mobility.
3.5.3.3. Switches
3.5.3.3.1. Store addresses sending packets to corresponding MAC addresses.
3.5.3.4. Router
3.5.3.4.1. Communication device used to create WANs.
3.5.3.5. Modem
3.5.3.5.1. Modulates digital signals to be sent through analog telephone lines.
3.5.3.6. Network Interface Card
3.5.3.6.1. Connects device to network.
3.6. Network Transmission Media
3.6.1. Physical
3.6.1.1. Twisted Pair (UTP)
3.6.1.1.1. 8 wires twisted into 4 separate pairs then twisted into a group
3.6.1.1.2. Twisting of wires reduces interference as wires don't run parallel to outside cables
3.6.1.2. Fibre Optic
3.6.1.2.1. Special glass pieces which transmit light
3.6.1.2.2. Immune to electromagnetic interference as information travels as light
3.6.1.2.3. Strands can only go one way, therefore 2 strands needed for both way communication
3.6.1.3. Coaxial Cable
3.6.1.3.1. Single copper wire which is surrounded by insulating material, a braided metal and plastic outer coating.
3.6.2. Wireless
3.6.2.1. Microwave
3.6.2.1.1. Requires line of sight without obstruction.
3.6.2.1.2. Satellite dishes upon high areas to ensure connection.
3.6.2.2. Infrared
3.6.2.2.1. Line of site required.
3.6.2.2.2. Only short distances.
3.6.2.2.3. Transmits through light waves.
3.6.2.3. Radio Waves
3.6.2.3.1. Bluetooth is an example that transfers up to 10m at 2mbps.
3.6.2.3.2. Cover both long and short distances.
3.7. Network Design
3.7.1. Logical
3.7.1.1. Considers factors of network protocols, speed, applications, network speed etc.
3.7.2. Physical
3.7.2.1. Physical design and communications lines of a network
3.8. Networks Connection Purposes
3.8.1. Resource sharing
3.8.1.1. To save money devices such as printers, scanners, internet connections and more are connected to a network instead of individually to each computer.
3.8.2. Remote service access
3.8.2.1. Internet ordering
3.8.2.2. Business-2-Business
3.8.2.3. Customers get validation feedback
3.8.3. Facilitating communications
3.8.3.1. Videoconferencing
3.8.3.2. Messaging
3.8.3.3. Chat rooms
3.8.3.4. Email
3.8.4. Data sharing/information.
3.8.4.1. Data on a network may be shared amongst the users of the network allowing for easy synchronisation.
4. TOPIC 3: Online Communities
4.1. Online Data Collection Pros
4.1.1. Timely
4.1.1.1. Data can always be collected through the persistant form
4.1.2. Validation
4.1.2.1. Collected results are the most accurate they may be as the form is specifically designed for limitations
4.2. Types of Online Communities
4.2.1. Social Networking
4.2.1.1. People exchange information in a social manner.
4.2.1.2. Accounts may or may not be created around aliases.
4.2.2. Interest and Project Based
4.2.2.1. Created around the idea of a topic or motive
4.2.2.2. Free membership for people to discuss things
4.2.3. Professional or Work Based
4.2.3.1. Stricter guidelines
4.2.3.2. Accounts created with real user details to maintain 'professional' aspect.
4.3. Audience Characteristics
4.3.1. Gender
4.3.2. Special Needs
4.3.3. Culture
4.3.4. Age
4.3.5. Access
4.4. Social Online Protocols
4.4.1. No abusive language
4.4.2. No commercial promotion
4.4.3. No SHOUTING or flaming or trolling
4.4.4. In the forum, do not start a new discussion topic as a reply to a post on a different topic
4.4.5. Posting inappropriate information
5. TOPIC 4: Databases
5.1. Normalisation
5.1.1. 1NF
5.1.1.1. Cells should only contain a single value
5.1.2. 2NF // 3NF
5.1.2.1. Fields should directly relate to the primary key. If they do not separate tables should be created with foreign keys connecting tables.
5.1.3. Pros
5.1.3.1. Reduces redundant data to make the solution find records faster
5.1.3.2. Increases data integrity making changes only need to be applied to a single record
5.1.3.3. Keeps the size of the database down and speeds up data retrieval
5.2. Data Types include
5.2.1. Text (alphanumeric)
5.2.2. Boolean (y/n)
5.2.3. Date
5.2.4. Integer (number)
5.3. Data relationships are
5.3.1. One to One
5.3.2. One to Many
5.3.3. Many to Many
5.4. Database Design Tools include
5.4.1. Data Structure Tables
5.4.1.1. Display name, data type and field details in a table
5.4.2. Entity Relationship Diagram
5.4.2.1. Graphically represent table relationships with fields and shapes
5.4.2.1.1. ERD Shapes
5.4.2.2. ERDs do not contain spaces within entities and do not require attributes be labeled as 'table'.
5.4.3. Data Structure Diagram
5.4.3.1. Displays relationships between individual tables
6. TOPIC 5: Information Systems and Organisations
6.1. Information System Elements
6.1.1. Equipment (Software/Hardware)
6.1.1.1. Hardware
6.1.1.1.1. System Unit
6.1.1.1.2. Communication Devices
6.1.1.1.3. Peripherals
6.1.1.2. Software
6.1.1.2.1. Application
6.1.1.2.2. Utility
6.1.2. Data (pre manipulation)
6.1.2.1. Data is entered as numbers, letters, words, images or sounds and is not meaningful until it has been processed and converted into information through manipulation.
6.1.2.1.1. Data may exists as two types
6.1.2.2. Data Requirements
6.1.2.2.1. Suitability
6.1.2.2.2. Reliability
6.1.2.2.3. Accuracy
6.1.2.2.4. Timeliness
6.1.2.2.5. Freedom from bias
6.1.3. Personnel (to oversee system)
6.1.3.1. Those who are users of the system.
6.1.3.2. Can be employees, customers, managers and technicians as well as others.
6.1.4. Procedures (to allow for manipulation
6.1.5. Information (Post data manipulation)
6.1.5.1. Information needs to be
6.1.5.1.1. Relevant
6.1.5.1.2. Complete
6.1.5.1.3. Accurate
6.1.5.1.4. Unbiased
6.1.5.1.5. Clarity of message
6.2. Decision Making
6.2.1. Strategic (Senior Management)
6.2.1.1. Long term
6.2.1.2. Made by CEO // President
6.2.2. Tactical (Middle Management)
6.2.2.1. Problems that affect organisation run time, ensure strategic decisions work.
6.2.2.2. Undergone within weeks or months.
6.2.2.3. Carried out by Directors // Managers.
6.2.3. Operational (Operational Management)
6.2.3.1. Day to day decisions such as staff management and stock management.
6.3. Information Structure
6.3.1. Detail Report
6.3.1.1. Communication of all assembled records
6.3.2. Summary Report
6.3.2.1. Brief versions of Detail Reports, make use of totals and averages.
6.3.2.2. Used by middle management.
6.3.3. Aggregate reports
6.3.3.1. Similar to Detail Reports except only detail one factor or subject
6.3.3.2. e.g sales of coke
6.3.4. Sample Report
6.3.4.1. Detailed information which provides senior management with overview.
6.3.5. Exception Report
6.3.5.1. Identifies data variation which may require action.
6.4. Information Problem causes
6.4.1. Information Errors
6.4.1.1. Information has errors either post or prior to manipulation which may lead the organisation to wasting time.
6.4.2. Does not meet user needs
6.4.2.1. System does not fully meet the needs of its users. For example a webpage loads on one users browser but not on the other users.
6.4.3. Dependence on old technology
6.4.3.1. Some information problems arise as a result of the lack of technology to solve it. Or the use of systems which are outdated and no longer are of optimal use.
6.5. Information Systems
6.5.1. Transaction Processing
6.5.1.1. Money and invoice systems
6.5.2. Office automation
6.5.2.1. Perform routine office tasks
6.5.2.2. e.g printing
6.5.3. Management Information
6.5.3.1. Generates reports to be viewed, usually built with TPS
6.5.4. Decision Support
6.5.4.1. Creates 'what if' scenarios with inputted data
6.5.5. Expert
6.5.5.1. Analyses data and produces decisions based on data
7. TOPIC 6: Spreadsheets
7.1. Design Tools
7.1.1. Structure Chart
7.1.1.1. Graphic display of how the contained worksheets relate to each other. Provides developer with an overall look to the solution.
7.1.2. Layout Diagram
7.1.2.1. General solution outlay with the inclusions of cell contents, validation rules, error messages, data types within cells etc.
7.1.3. Formula List
7.1.3.1. To display which formulas do what and how, written in plain english.
7.2. Design Elements
7.2.1. Proportion
7.2.1.1. Visual hierarchy of objects on the page as well as the sizing of specific objects with respect to their importance.
7.2.2. Orientation
7.2.2.1. The location and alignment of page objects.
7.2.3. Clarity and consistency
7.2.3.1. How easily visual elements can be distinguished from each other as well as the consistent use of font and page design.
7.2.4. Colour and Contrast
7.2.4.1. Use of colours on the page which would allow them to be seen easily. Contrast between colours should be at their maximum for ease of viewing. Additionally the amount of white space should be recognised.
7.3. Screen Characteristics
7.3.1. Usability
7.3.1.1. Long screens requiring scrolling should be avoided as well as unnecessary buttons.
7.3.2. Font
7.3.2.1. Keep to around 2 fonts, one for headings and another for body.
7.3.2.2. Serif fonts for large text chunks
7.3.3. Accessibilty
7.3.3.1. Information needs to be able to be accessed easily
7.3.3.2. Layouts should be useable on a number of devices with varying resolutions
7.3.3.3. No technical language that is hard to understand
7.3.3.4. Should be easy to view for the vision impaired
7.3.3.5. Should be culturally accepting so people of different races may easily use the solution as well
7.3.4. Appropiateness and Relevence
7.3.4.1. Information should be useful to its purpose
7.3.4.2. Language used should be that of which the target audience of the solution will understand
8. TOPIC 7: Information Management
8.1. Laws
8.1.1. Information Privacy Act 2000 (VIC)
8.1.1.1. Creation of privacy comissioner
8.1.1.2. Victorian addition of the Privacy Act 1988
8.1.1.3. Only covers government sector NO PRIVATE.
8.1.2. Privacy Act 1988 (Federal)
8.1.2.1. Protection regarding the government collection of tax file numbers
8.1.2.2. Websites must provide a privacy policy explaining gathered data.
8.1.2.3. For private organisations to be subject to this act they need to either turn over 3m a year, hold any non employee health information or trade personal information for money.
8.1.2.4. Data collected must only be used for its collection purpose
8.1.2.5. Information is to be kept for the time that it is needed, in this time it must be kept up to date to which the person it is about has access
8.1.3. Health Records Act 2001 (VIC)
8.1.3.1. Covers both private and public sector health records
8.1.3.2. Ensures health information cant be disclosed to third parties without consent.
8.1.3.3. Use of personal health information may exist in the case where the person is unable to consent due to illness, a serious public threat exists or research is to be done with the interest of the public.
8.1.4. Copyright Act (1968)
8.1.4.1. Automatic and free
8.1.4.2. Covers texts, music, videos, broadcasts and computer progrmas
8.1.4.3. Does NOT cover ideas, concepts, names etc.
8.1.4.4. Copyright applies for 70 years plus the lifetime of its creator
8.1.4.5. Educational organisations as well as the government are able to by pass copyright in some circumstances when making copies.
8.1.4.6. Amended in 2006 to include electronic items
8.1.5. Charter Of Human Rights And Responsibilities
8.1.5.1. Protection of privacy and reputation
8.1.5.2. Freedom of thought, conscience and the ability to believe in something as well as practice it
8.1.5.3. Freedom of expression as long as it isn't interrupting national security
8.1.6. Spam Act (2003)
8.1.6.1. Protection upon the receiving of unsolicited electronic, commercial messages.
8.1.6.2. Messages must only be sent with the consent of the reciever
8.1.6.3. The message must include an option to unsubscribe
8.2. National Privacy Principles
8.2.1. 1. Collected information must be for a lawful purpose and be necessary to that given purpose
8.2.2. 2. The collector of the information must detail why the information has been collected
8.2.3. 3. Collected information must be relevant to its collection purpose and hence be kept up to date and complete
8.2.4. 4. Information must be kept secure to which it is safe guarded from loss, disclosure or unauthorised access
8.2.5. 5. Collectors must ensure that the purpose of collection is made clear as that the person who has had their information collected understands how they can access their information
8.2.6. 6. Individuals are able to access their held information
8.2.7. 7. Records are to be accurate and kept up to date as well as amended if errors are found
8.2.8. 8. Before the information can be used it must be accurate, complete and relevant to its purpose use
8.2.9. 9. Information must only be kept if it is relevent
8.2.10. 10. Information must only be used for its collection purpose
8.2.11. 11. Personal information must not be disclosed without consent ---
8.3. Threats to Data
8.3.1. Intentional
8.3.1.1. Viruses
8.3.1.1.1. Removing computer functionality through block connections or taking up memory
8.3.1.2. Information Theft
8.3.1.2.1. The theft of digital information from companies
8.3.1.2.2. May come as a result of a cracker with a terminal or simply an informant with physical access
8.3.1.3. Hacking/Cracking
8.3.1.3.1. The process of breaking into information systems and looking at confidential material. A cracker will do this with the intention of modifying files.
8.3.1.4. File Tampering
8.3.1.4.1. May occur when data is sent of signals
8.3.1.4.2. May occur with electronically stored data on a server
8.3.1.5. Hardware Theft
8.3.2. Accidental
8.3.2.1. User Error
8.3.2.1.1. A user doesn't shutdown the system properly
8.3.2.1.2. Copying over old file versions to new ones
8.3.2.2. Equipment failure
8.3.2.2.1. General hardware damage through either electrical variation, smoke, fire, water, breakage etc.
9. TOPIC 8: Security and Ethical Considerations
9.1. Security Software
9.1.1. Firewalls
9.1.1.1. Filter information coming through internet connections through port blocking
9.1.1.2. Flagged packets do not enter
9.1.2. Malware
9.1.2.1. Spyware
9.1.2.1.1. Uses cookies to track visited internet sites
9.1.2.2. Trojans
9.1.2.2.1. Appear as safe exe. files but create backdoor access to systems
9.1.2.3. Viruses
9.1.2.3.1. Modify and delete files as well as consume memory
9.1.2.4. Worm
9.1.2.4.1. Replicates itself taking up storage
9.1.3. Encryption
9.1.3.1. Scrambling of data to make it unreadable without the sufficient key to access it.
9.2. Back-Ups
9.2.1. Incremental
9.2.1.1. Works in conjunction with the full backup. Will only backup files changed since the last consequent INCREMENTAL backup.
9.2.2. Full
9.2.2.1. Whole data backup, fastest and easiest restoration.
9.2.3. Differential
9.2.3.1. Used with a full backup, will only backup files which have been changed from the previous full backup
9.2.4. RAID system (Redundant Array of Inexpensive Disks)
9.2.4.1. Several drives which appear as a single drive and instead have their information stored amongst them all.
9.2.4.2. Means if a single drive fails the other drives may still be operational and not all data will be lost.
9.3. Surveillance Technology
9.3.1. Packet Sniffers
9.3.1.1. Monitor packet contents through the filtration of certain data elements or phrases.
9.3.2. Audit Trail
9.3.2.1. Network records of when certain users logged in and what files they accessed.
9.3.3. Closed Circuit Television (CCTV)
9.4. Disaster Recovery Plans
9.4.1. Emergency
9.4.1.1. Steps which are taken during the course of a natural disaster.
9.4.1.2. Made up of contact details of those to be notified, procedures regarding system shutdown and evacuation of personnel.
9.4.2. Backup
9.4.2.1. Include the location of backup data and equipment, personnel required to do specific tasks.
9.4.3. Recovery
9.4.3.1. Have the aim of restoring the system to a functioning stage.
9.4.3.2. Identified systems which are paramount to the company and should be brought online first.
9.4.4. Test
9.4.4.1. Has the purpose of creating a number of simulations which would test the company to ensure they are prepared for an actual disaster.
9.5. Security Hardware
9.5.1. Biometrics
9.5.1.1. Protection through the recognition of human characteristics
9.5.1.2. May be speech recognition, iris recognition, hand written recognition
9.5.2. Swipe Cards
9.5.2.1. Physical card with a users details on it as well as a magnetic strip that allows them to gain access to areas as well as do certain authorisation things.
9.5.3. Security Token
9.5.3.1. Method of two step verification in which a card is taken around that displays a constantly changing number needed to log in alongside account information.
9.5.4. Surge Protector
9.5.4.1. Monitors electrical current coming from a power supply denies any large variances that may happen
9.5.5. UPS (uninterruptible power supply)
9.5.5.1. Surge protector with in-built power supply which in the case that the surge protector fails the battery will sustain enough power (a few minutes worth) for the system to be shutdown safely.
